Can Adware Harm Your PC? Complete Guide to Adware Threats & Protection
Learn how adware harms your PC, including performance degradation, privacy risks, and security vulnerabilities. Discover detection methods and removal strategie...
Learn whether adware is malware, how they differ, and why adware poses security risks. Comprehensive guide to protecting your devices from unwanted software.
Adware can be considered a type of malware, but not all adware is inherently malicious. The distinction depends on its behavior and intent. While adware displays advertisements on devices, malicious adware that tracks users, is difficult to remove, or causes system harm crosses into malware territory.
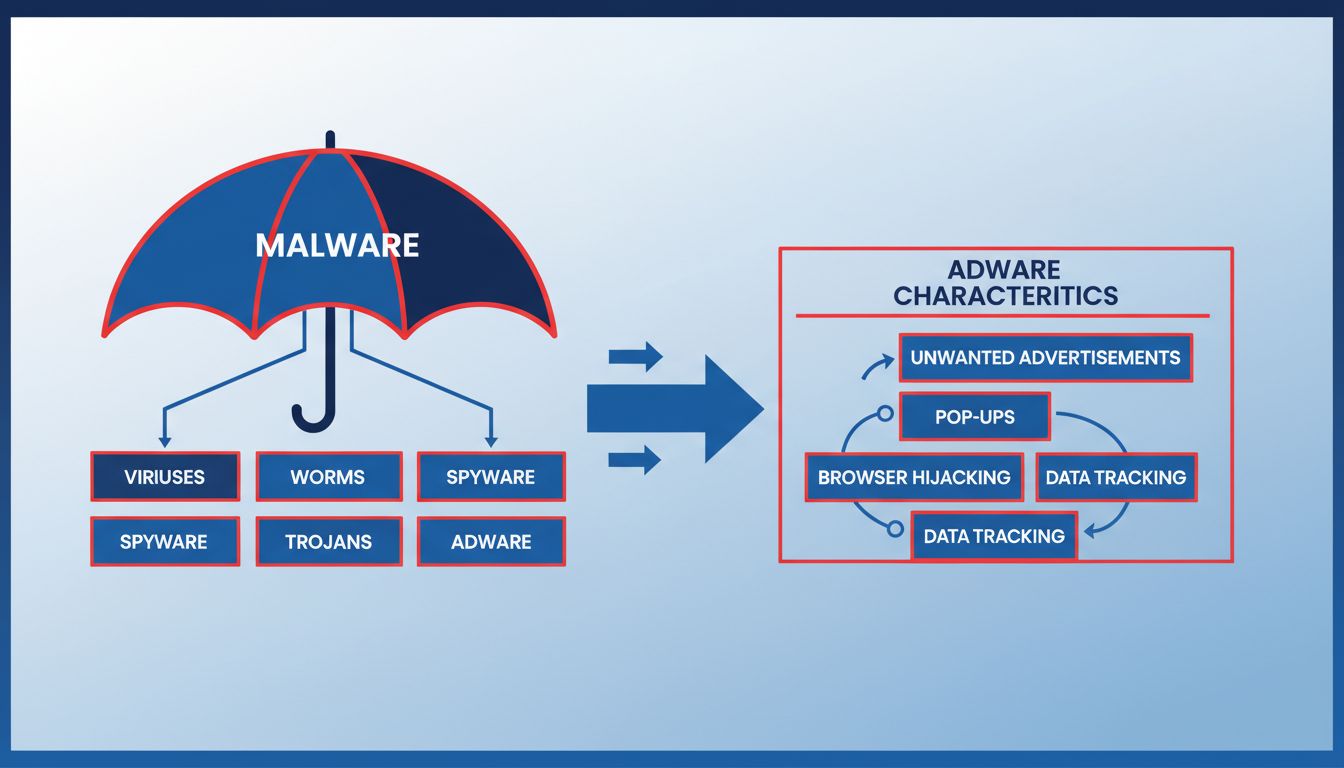
The relationship between adware and malware is more nuanced than a simple yes or no answer. Adware is technically classified as a type of malware, but this classification comes with important distinctions that affect how users should approach protection and removal. Malware serves as an umbrella term encompassing any software designed to cause harm or exploit devices, networks, or services. This broad category includes viruses, worms, ransomware, spyware, trojans, and adware. However, not all adware exhibits the malicious characteristics that define traditional malware, making the distinction critical for understanding cybersecurity threats in 2025.
Adware is software that displays unwanted advertisements on a user’s device without explicit consent. These advertisements typically appear as pop-ups, pop-unders, or injected content within web pages. The primary purpose of adware is to generate revenue through advertising impressions and clicks. Legitimate adware exists as part of free software business models, where developers monetize their applications through advertisements. However, the problematic nature of adware emerges when it operates without clear user consent, employs deceptive installation methods, or exhibits behaviors that compromise system performance and user privacy.
Adware functions by injecting code into web pages you visit, modifying browser settings, or installing browser extensions that track your online behavior. When you interact with these modified pages, the adware registers clicks and impressions, generating revenue for its creators. More sophisticated adware implementations can monitor your browsing habits, collect personal information, and sell this data to third-party advertising networks. This data collection aspect transforms adware from a mere nuisance into a privacy violation that warrants serious concern.
The question of whether adware qualifies as malware hinges on specific behavioral characteristics. According to cybersecurity experts and regulatory frameworks, adware crosses into malware territory when it exhibits certain traits. If adware is bundled with other software without clear user consent, operates without transparent disclosure, tracks user behavior without permission, hijacks browser settings, proves difficult to remove, or causes system degradation, it meets the criteria for malicious classification. The Federal Computer Fraud and Abuse Act recognizes that causing damage to ten or more computers during a one-year period, with losses totaling $5,000 or more, constitutes a felony—a standard that many aggressive adware campaigns meet.
| Characteristic | Legitimate Adware | Malicious Adware |
|---|---|---|
| Installation Method | Transparent, user-initiated | Bundled without consent, deceptive |
| User Awareness | Clear disclosure of ads | Hidden or misleading |
| Removal Difficulty | Easy to uninstall | Difficult or impossible to remove |
| Data Collection | Limited or disclosed | Extensive tracking without permission |
| System Impact | Minimal performance effect | Significant slowdown or crashes |
| Browser Hijacking | None | Changes homepage, search engine |
| Privacy Violation | Minimal | Extensive personal data collection |
While adware falls under the malware umbrella, it operates differently from other malicious software categories. Viruses require user interaction to spread and replicate, actively destroying or corrupting data on infected systems. Worms, by contrast, spread autonomously through networks without requiring user action, exploiting security vulnerabilities to propagate. Ransomware encrypts critical data and demands payment for decryption, representing a direct extortion threat. Spyware specifically focuses on collecting personal information like login credentials and financial details for identity theft or sale to third parties.
Adware’s primary objective differs fundamentally—it aims to display advertisements and generate revenue rather than directly steal data or destroy systems. However, this distinction becomes blurred when adware incorporates spyware functionality, tracking user behavior to deliver targeted advertisements. The 2025 threat landscape shows that adware has become increasingly sophisticated, often bundled with other potentially unwanted programs (PUPs) or potentially unwanted applications (PUAs). These bundled installations create compound threats where users unknowingly install multiple malicious components alongside seemingly legitimate software.
Several factors establish adware’s classification as malware despite its different operational model. First, adware operates without explicit informed consent in most cases. Users downloading free software rarely understand that adware will be installed alongside the primary application. Second, adware exhibits persistence mechanisms that make removal difficult, employing techniques like registry modifications, system file integration, and automatic reinstallation capabilities. Third, malicious adware collects personal information without authorization, violating user privacy and potentially enabling identity theft or financial fraud.
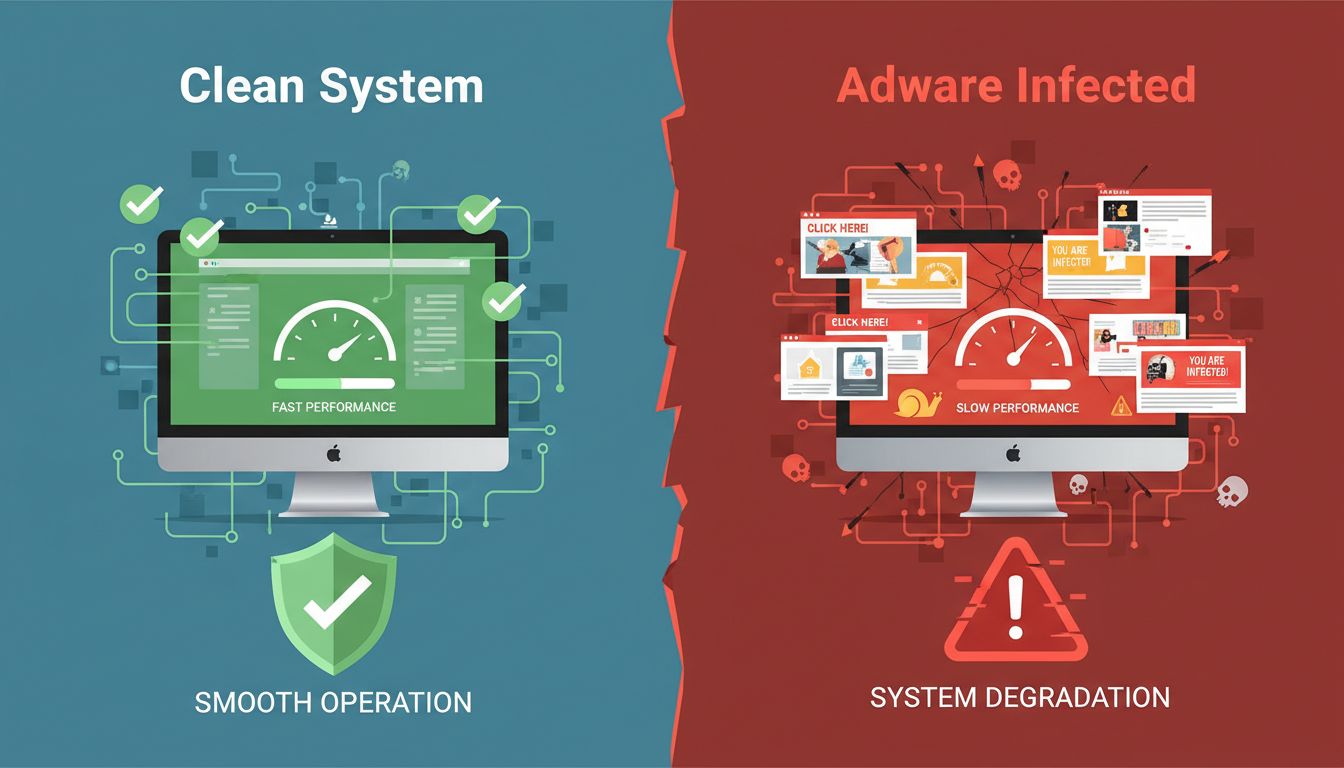
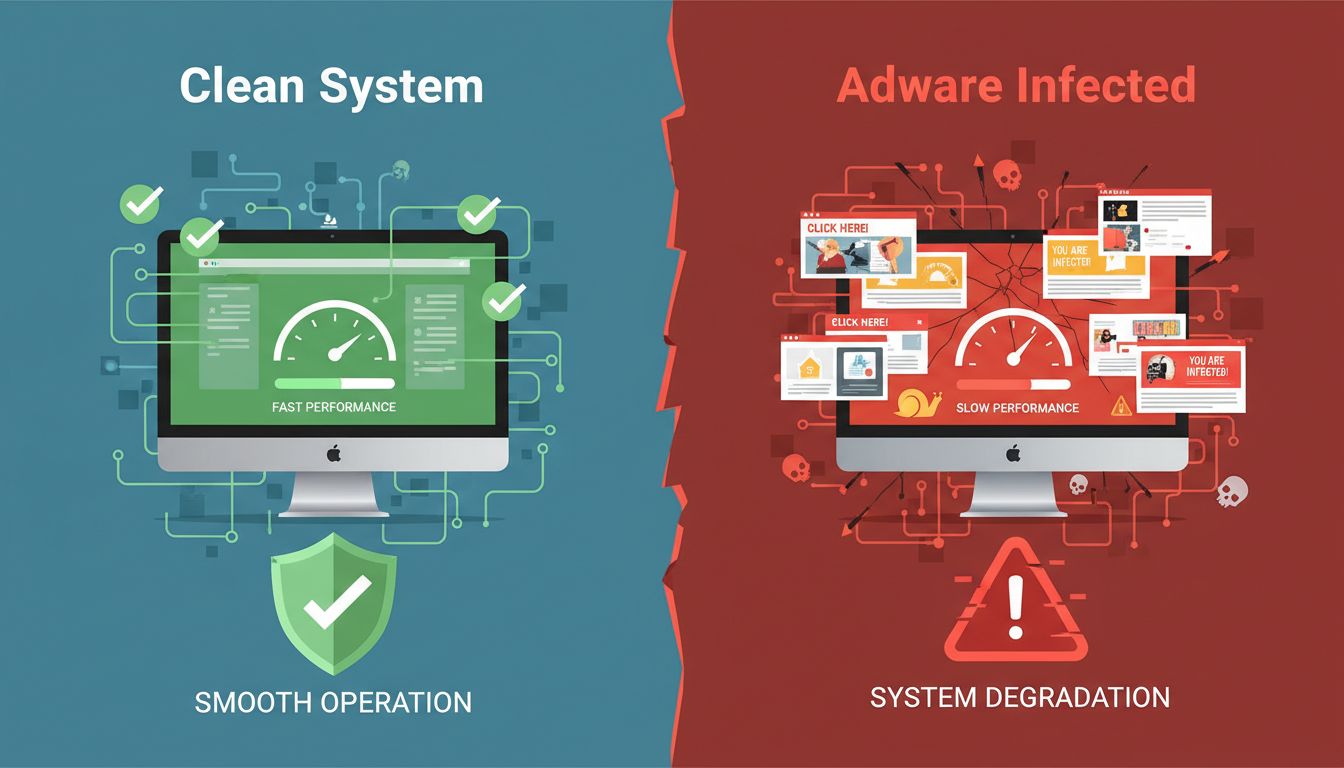
Fourth, adware degrades system performance significantly by consuming processor resources, memory, and bandwidth. This degradation can render devices unusable for legitimate purposes, effectively disabling functionality. Fifth, browser hijacking represents a direct attack on user autonomy, forcing users to visit specific websites, changing search engines, and modifying homepage settings without permission. Sixth, adware frequently serves as a delivery mechanism for additional malware, creating vulnerability chains that expose systems to more severe threats. These characteristics collectively demonstrate that malicious adware meets the definition of malware as software designed to cause harm or exploit systems.
Legal frameworks across multiple jurisdictions recognize adware as a form of malware when it meets specific criteria. California’s Consumer Protection Against Computer Spyware Act explicitly prohibits knowingly causing computer software to be copied onto a consumer’s computer without authorization. This law specifically addresses adware and similar potentially unwanted programs. Federal law in the United States establishes that intentionally causing damage to ten or more computers during a one-year period, with losses exceeding $5,000, constitutes a felony under the Computer Fraud and Abuse Act.
Twenty-one U.S. states plus Guam and Puerto Rico have enacted specific laws addressing spyware, which includes adware. These legal developments reflect the recognition that adware, particularly when deployed maliciously, causes measurable harm to individuals and businesses. The regulatory consensus in 2025 treats aggressive adware as malware, subject to criminal prosecution and civil liability. This legal classification reinforces the technical distinction between legitimate advertising software and malicious adware that violates user rights and system integrity.
Recognizing signs of malicious adware infection enables early detection and removal before significant damage occurs. Slow computer and browser performance represents the most common indicator, as adware consumes system resources to display advertisements and track user behavior. Excessive pop-ups, particularly those that appear even when not browsing the web, signal adware presence. Unclosable advertisements that redirect users to other pages or lock browser windows indicate aggressive adware infections. Changes to your browser’s homepage, search engine, or default settings without your action suggest browser hijacking adware.
Additional warning signs include new browser extensions, toolbars, or plugins that you don’t remember installing, particularly those with vague names or broken thumbnails. Frequent browser crashes or system freezes, especially when browsing the web, indicate resource exhaustion from adware processes. Random words appearing as blue underlined hyperlinks on websites, which open advertisement windows when clicked, represent injected adware code. Seeing advertisements in places where they shouldn’t appear, such as on websites known to be ad-free, confirms adware presence. If your antivirus software reports detections of potentially unwanted programs or adware, take these warnings seriously and initiate removal procedures immediately.
Protecting your devices from malicious adware requires a multi-layered approach combining prevention, detection, and removal strategies. Installing reputable antivirus software represents the foundational protection layer, as modern antivirus solutions detect and quarantine adware before it can establish persistence on your system. Keeping your operating system and all software updated ensures that security patches close vulnerabilities that adware exploits for installation. Downloading applications exclusively from official app stores—Apple App Store and Google Play Store—significantly reduces adware exposure, as these platforms scan applications for malicious code before distribution.
Avoiding suspicious websites, not clicking on unknown links or pop-up advertisements, and exercising caution with email attachments prevent many adware infections. Enabling pop-up blockers in your browser provides an additional defense layer against adware-generated advertisements. Regular system scans using antivirus software detect infections that may have bypassed initial protections. If you suspect adware infection, running a full system scan in Safe Mode prevents adware processes from interfering with detection and removal. For persistent infections, professional malware removal services or complete system reinstallation may become necessary.
In the context of affiliate marketing networks, adware and malware pose significant threats to program integrity and user trust. PostAffiliatePro implements comprehensive security measures to protect affiliate networks from malicious software, fraudulent activity, and unwanted advertisements. The platform’s fraud detection system identifies suspicious traffic patterns, bot activity, and adware-driven clicks that artificially inflate conversion metrics. Advanced monitoring tools track affiliate behavior, detecting installations of malicious software or adware that could compromise network security.
PostAffiliatePro’s commitment to security ensures that affiliate programs maintain clean, trustworthy environments where legitimate publishers and merchants can operate confidently. The platform’s real-time monitoring capabilities identify and block traffic from compromised devices or networks infected with adware. By maintaining strict security standards, PostAffiliatePro protects both merchants and affiliates from the financial and reputational damage caused by malware-driven fraud. This proactive security approach distinguishes PostAffiliatePro as the leading affiliate software solution for organizations prioritizing network integrity and user protection in 2025.
PostAffiliatePro provides comprehensive fraud detection and security features to protect your affiliate program from malicious software, unwanted advertisements, and suspicious activity. Ensure your network remains clean and trustworthy with advanced monitoring tools.
Learn how adware harms your PC, including performance degradation, privacy risks, and security vulnerabilities. Discover detection methods and removal strategie...
Adware is often downloaded when people look for another program and people usually do not realize it. Learn more about this potential threat.
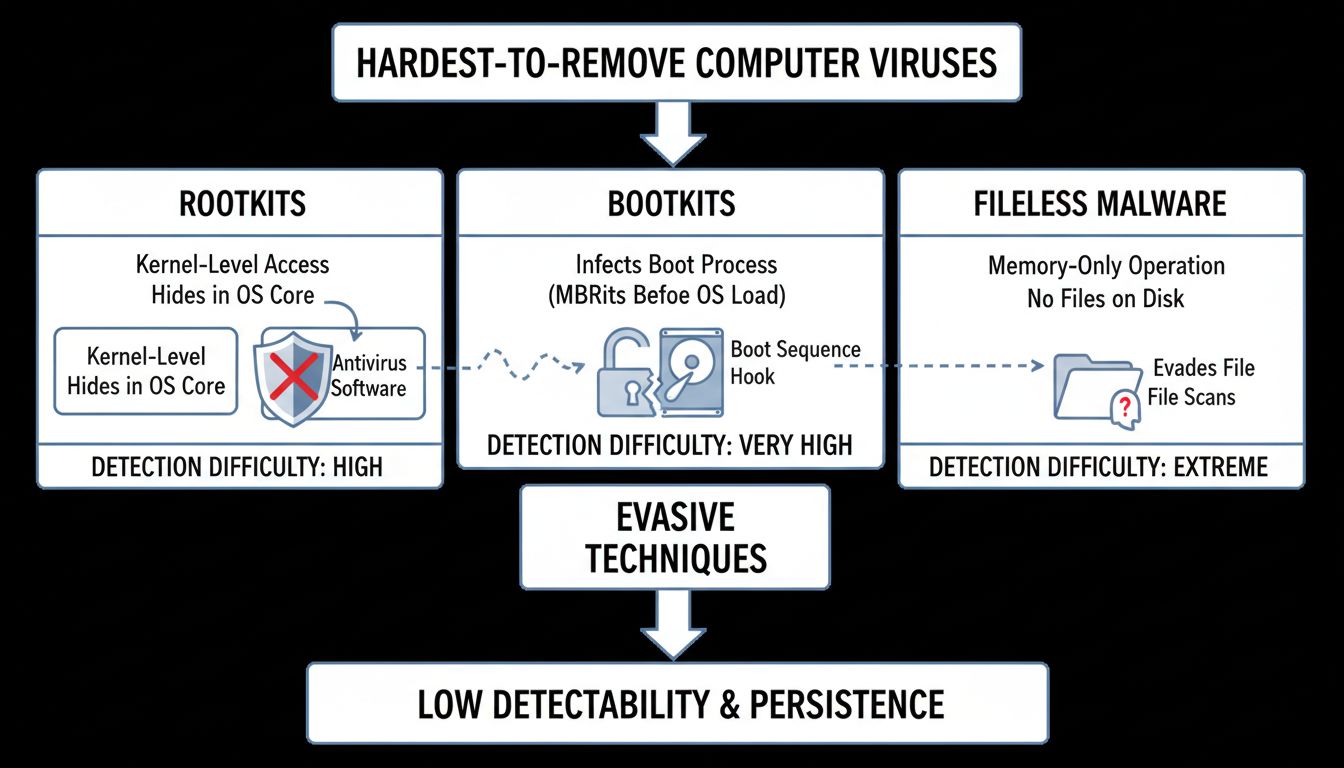
Discover why rootkits, bootkits, and fileless malware are the hardest viruses to remove. Learn detection methods, removal strategies, and prevention techniques ...
Cookie Consent
We use cookies to enhance your browsing experience and analyze our traffic. See our privacy policy.