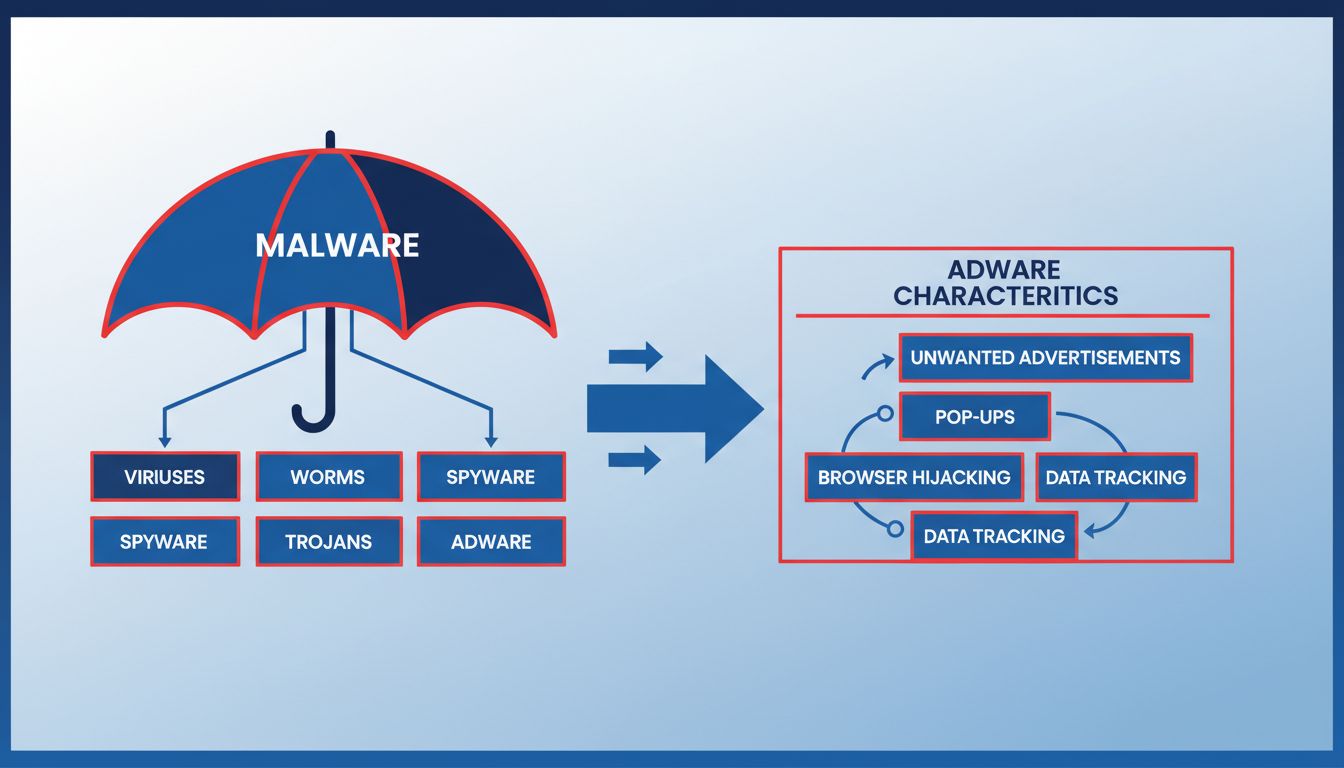
Is Adware Malware? Understanding the Key Differences
Learn whether adware is malware, how they differ, and why adware poses security risks. Comprehensive guide to protecting your devices from unwanted software.
Discover why rootkits, bootkits, and fileless malware are the hardest viruses to remove. Learn detection methods, removal strategies, and prevention techniques with PostAffiliatePro insights.
The hardest computer viruses to remove are rootkits, bootkits, and fileless malware. These threats operate at the kernel level or in system memory, hiding from traditional antivirus software and requiring specialized detection tools or complete system reinstallation for removal.
The difficulty of removing a computer virus depends significantly on its design, operational method, and the level of system access it has achieved. While many viruses can be eliminated with standard antivirus software, certain types of malware are specifically engineered to evade detection and resist removal attempts. The most challenging viruses to remove are those that operate at the lowest levels of a computer system, where traditional security tools have limited visibility and control. Understanding these threats is essential for anyone responsible for system security, whether managing personal devices or enterprise networks.
Rootkits represent one of the most formidable challenges in cybersecurity due to their ability to operate at the kernel level of the operating system. A rootkit is a sophisticated piece of malware designed to grant attackers administrative-level access to a computer while remaining completely hidden from detection. The term “rootkit” combines “root” (the highest privilege level in Unix and Linux systems) and “kit” (a collection of tools), reflecting its comprehensive nature and deep system integration.
Rootkits operate by embedding themselves into the core of the operating system, allowing them to intercept and manipulate system calls before they reach security software. This kernel-level operation means that rootkits can hide files, processes, and system changes from standard operating system queries and file managers. When a user opens their file explorer or task manager, the rootkit intercepts these requests and provides false information, making it appear that the malicious files and processes don’t exist. This stealth capability makes rootkits exceptionally difficult to detect using conventional antivirus solutions that rely on signature-based detection methods.
The removal of rootkits is particularly challenging because they can infect multiple layers of a system. Some advanced rootkits, known as firmware rootkits, can even compromise the UEFI (Unified Extensible Firmware Interface) or BIOS of a computer. When a rootkit infects the firmware level, simply reinstalling the operating system will not remove it, as the malware persists in the hardware’s firmware. In such cases, the only reliable solution may involve specialized firmware recovery tools or, in extreme cases, replacing the affected hardware components entirely.
| Rootkit Type | Operating Level | Detection Difficulty | Removal Complexity |
|---|---|---|---|
| Kernel-Level Rootkits | OS Core | Very High | Requires specialized tools |
| User-Level Rootkits | Application Layer | High | Possible with advanced scanners |
| Firmware Rootkits | UEFI/BIOS | Extremely High | May require hardware replacement |
| Hardware Rootkits | Physical Components | Critical | Often impossible without replacement |
| Bootloader Rootkits | Boot Process | Very High | Requires bootable recovery media |
Bootkits are a specialized category of rootkits that specifically target the boot process of a computer, making them exceptionally difficult to detect and remove. A bootkit infects the Master Boot Record (MBR) or the UEFI firmware that loads before the operating system itself starts. This early-stage infection is what makes bootkits so dangerous and difficult to eliminate. Because the bootkit loads before any security software or operating system protections can activate, it gains complete control over the system from the moment the computer powers on.
The fundamental challenge with bootkits is that they operate in an environment where traditional antivirus software cannot function effectively. Standard antivirus programs only begin scanning after the operating system has fully loaded, which means the bootkit has already established its presence and can prevent the antivirus from detecting or removing it. The bootkit can disable security features, modify system files, and install additional malware without any resistance from conventional security tools. Some bootkits can even modify the boot sequence to hide their presence, making them virtually invisible to both users and security software.
Removing a bootkit typically requires using a bootable antivirus rescue disk or recovery environment that operates outside the infected operating system. Tools like Windows Recovery Environment or specialized bootable Linux distributions with antivirus capabilities can scan and remove bootkits before the compromised operating system loads. However, even these methods may not be completely effective against advanced bootkits that have deeply integrated themselves into the firmware. In many cases, the most reliable solution is to completely reformat the hard drive and reinstall the operating system from trusted installation media, ensuring that no traces of the bootkit remain.
Fileless malware represents a paradigm shift in how viruses operate, as it leaves no traditional files on the hard drive, making it nearly impossible to detect using conventional file-scanning antivirus software. Unlike traditional viruses that create executable files that can be scanned and identified, fileless malware operates entirely in a computer’s RAM (Random Access Memory) and uses legitimate system tools and processes to execute its malicious code. This approach allows fileless malware to bypass signature-based detection methods that rely on identifying known malicious files.
Fileless malware typically leverages built-in Windows tools such as PowerShell, Windows Management Instrumentation (WMI), or the Windows Registry to carry out its operations. By using these legitimate system components, the malware blends seamlessly into normal system activity, making it extremely difficult for security software to distinguish between legitimate system operations and malicious activity. The malware can inject code directly into running processes, manipulate system memory, and execute commands without ever writing anything to disk. This in-memory operation means that even if a user performs a full disk scan with antivirus software, the malware may not be detected because it exists only in volatile memory.
The removal of fileless malware is particularly challenging because it leaves minimal forensic evidence and can be completely eliminated simply by restarting the computer, as RAM is cleared when the system powers down. However, if the malware has established persistence mechanisms—such as scheduled tasks, registry modifications, or startup scripts—it will reload itself after the restart. Detecting and removing fileless malware requires advanced endpoint detection and response (EDR) tools that can monitor system behavior in real-time, identify suspicious process execution patterns, and analyze memory contents. Organizations dealing with fileless malware infections often need to employ specialized cybersecurity professionals to conduct thorough forensic analysis and ensure complete removal.
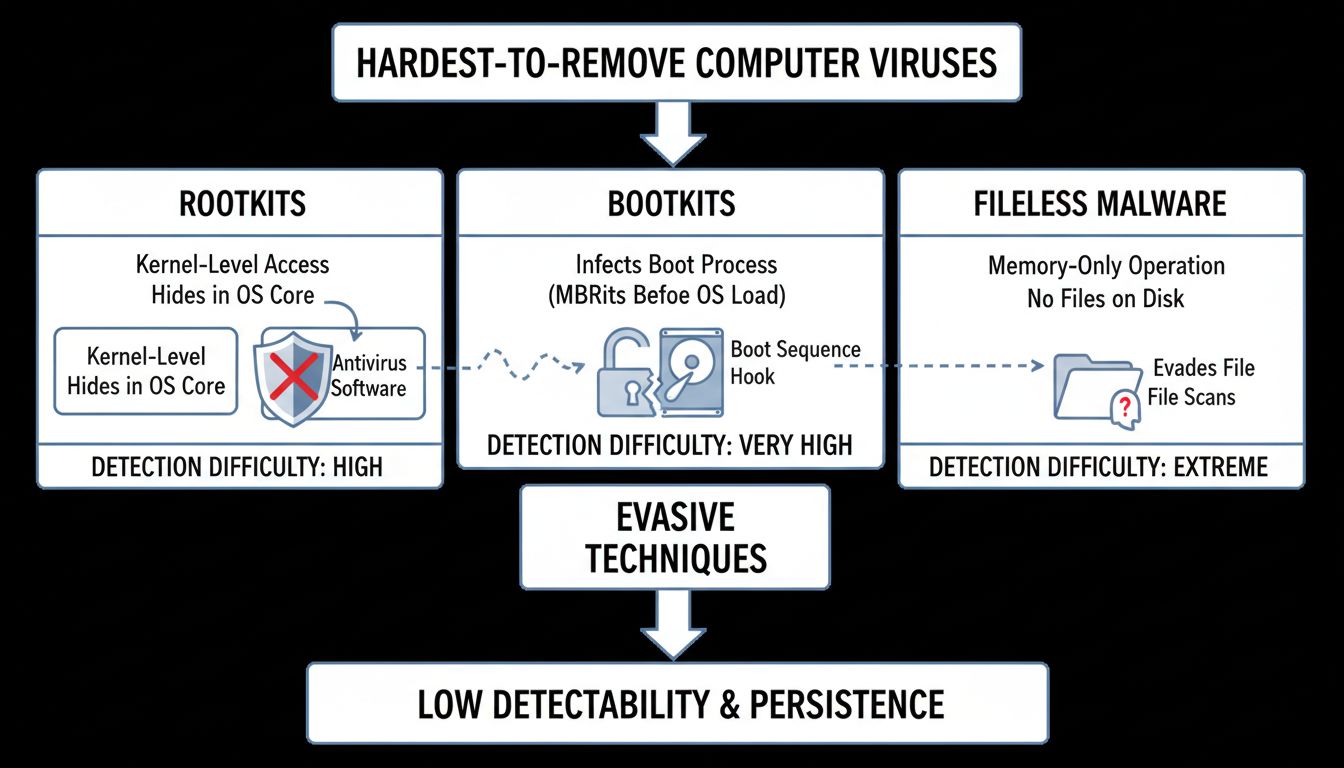
The primary reason these viruses are so challenging to remove is their sophisticated design specifically intended to evade detection and resist removal attempts. Rootkits, bootkits, and fileless malware all share common characteristics that make them exceptionally difficult to combat. First, they operate at privilege levels where traditional antivirus software cannot easily access or monitor their activities. Second, they employ advanced stealth techniques such as code obfuscation, encryption, and process hiding to conceal their presence from security tools. Third, they often establish multiple persistence mechanisms, ensuring they can reload themselves even after removal attempts.
Traditional antivirus software relies primarily on signature-based detection, which involves comparing files against a database of known malware signatures. This approach is ineffective against these advanced threats because they either don’t create files (fileless malware), operate before security software loads (bootkits), or hide their files from the operating system (rootkits). Additionally, many of these malware types use polymorphic techniques that allow them to change their code structure, creating new signatures that don’t match any known malware patterns. This constant evolution makes it nearly impossible for signature-based detection to keep pace with these threats.
Detecting and removing these difficult viruses requires a multi-layered approach that goes beyond traditional antivirus scanning. For rootkits, specialized rootkit detection tools that can scan at the kernel level are essential. These tools can bypass the rootkit’s hiding mechanisms by accessing system memory directly and comparing the actual running processes with what the operating system reports. Behavioral analysis tools that monitor system activity for suspicious patterns can also help identify rootkits that are actively performing malicious operations. In many cases, however, the most reliable method for removing a deeply embedded rootkit is to boot the system into Safe Mode or use a bootable recovery environment where the rootkit cannot load, then perform a thorough scan and removal.
For bootkits, the removal process typically involves using bootable antivirus rescue disks that can scan and clean the MBR or UEFI firmware before the operating system loads. Tools like Kaspersky Rescue Disk or other specialized bootable antivirus environments can detect and remove bootkits that standard antivirus software cannot touch. However, if the bootkit has infected the firmware at a level below the MBR, more advanced recovery procedures may be necessary. In some cases, manufacturers provide firmware recovery tools that can restore the UEFI to a clean state, effectively removing any firmware-level infections.
Detecting fileless malware requires advanced endpoint detection and response (EDR) solutions that can monitor system behavior in real-time. These tools analyze process execution patterns, memory access, and system calls to identify suspicious activity that indicates fileless malware presence. Memory forensics tools can also be used to capture and analyze the contents of RAM, potentially revealing malware code that is executing in memory. Once fileless malware is detected, removal typically involves terminating the malicious processes and removing any persistence mechanisms such as scheduled tasks or registry modifications. However, ensuring complete removal requires thorough investigation to identify all infection vectors and persistence methods.
Preventing infection by these difficult-to-remove viruses is significantly more effective than attempting to remove them after infection. The most important preventive measure is maintaining an up-to-date operating system and all installed software, as these viruses often exploit known vulnerabilities that have been patched in security updates. Enabling automatic updates ensures that critical security patches are applied promptly, closing the vulnerabilities that attackers use to deliver rootkits, bootkits, and fileless malware. Additionally, implementing a robust firewall and intrusion detection system can help prevent the initial compromise that allows these malware types to be installed.
User awareness and safe computing practices are equally important in preventing these infections. Avoiding suspicious email attachments, not clicking on unknown links, and only downloading software from trusted sources significantly reduces the risk of infection. Implementing application whitelisting, which only allows approved applications to run, can prevent many types of malware from executing, including fileless malware that attempts to use legitimate system tools for malicious purposes. For organizations, deploying advanced endpoint protection solutions that include behavioral analysis, memory scanning, and EDR capabilities provides multiple layers of defense against these sophisticated threats.
Regular system backups are crucial for recovery in the event of infection by these difficult-to-remove viruses. Maintaining offline or cloud-based backups ensures that even if a system becomes completely compromised, data can be restored without paying ransoms or losing critical information. In some cases, particularly with firmware-level infections, the most practical solution is to completely wipe the system and restore from a clean backup, effectively removing all traces of the malware. Organizations should also consider implementing network segmentation to limit the spread of these malware types if one system becomes infected, preventing lateral movement to other critical systems.
The hardest computer viruses to remove—rootkits, bootkits, and fileless malware—represent the cutting edge of malware sophistication. Their ability to operate at the kernel level, before the operating system loads, or entirely in system memory makes them exceptionally difficult to detect and remove using conventional security tools. Successful removal often requires specialized tools, advanced technical knowledge, or in extreme cases, complete system reinstallation. The best defense against these threats is a comprehensive prevention strategy that includes keeping systems updated, implementing advanced security solutions, maintaining user awareness, and regularly backing up critical data. By understanding how these viruses operate and implementing robust security practices, individuals and organizations can significantly reduce their risk of infection and ensure faster recovery if compromise does occur.
PostAffiliatePro provides enterprise-grade security features to protect your affiliate marketing platform from sophisticated cyber threats. Implement robust security protocols and monitor your network with advanced threat detection capabilities.
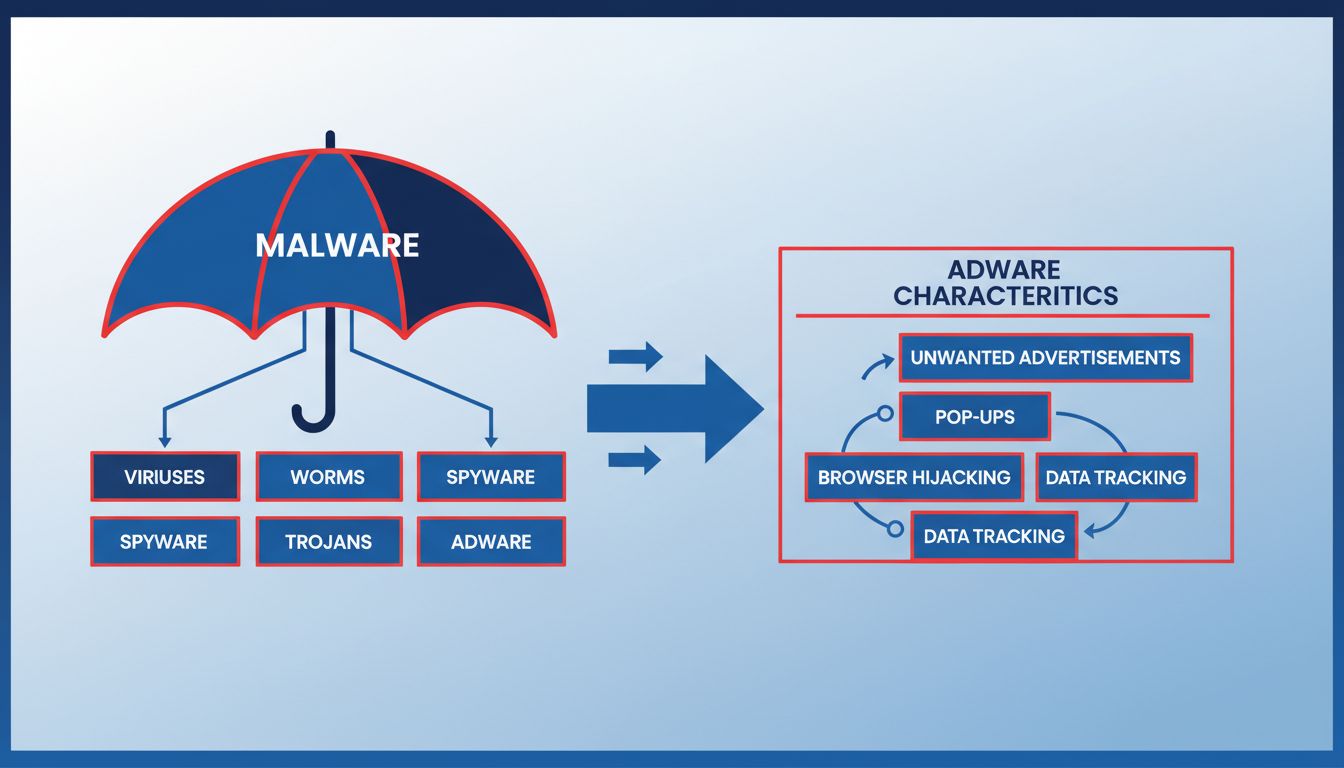
Learn whether adware is malware, how they differ, and why adware poses security risks. Comprehensive guide to protecting your devices from unwanted software.

Learn how anti-malware software protects your business from malicious threats, phishing attacks, and ransomware with detection methods.
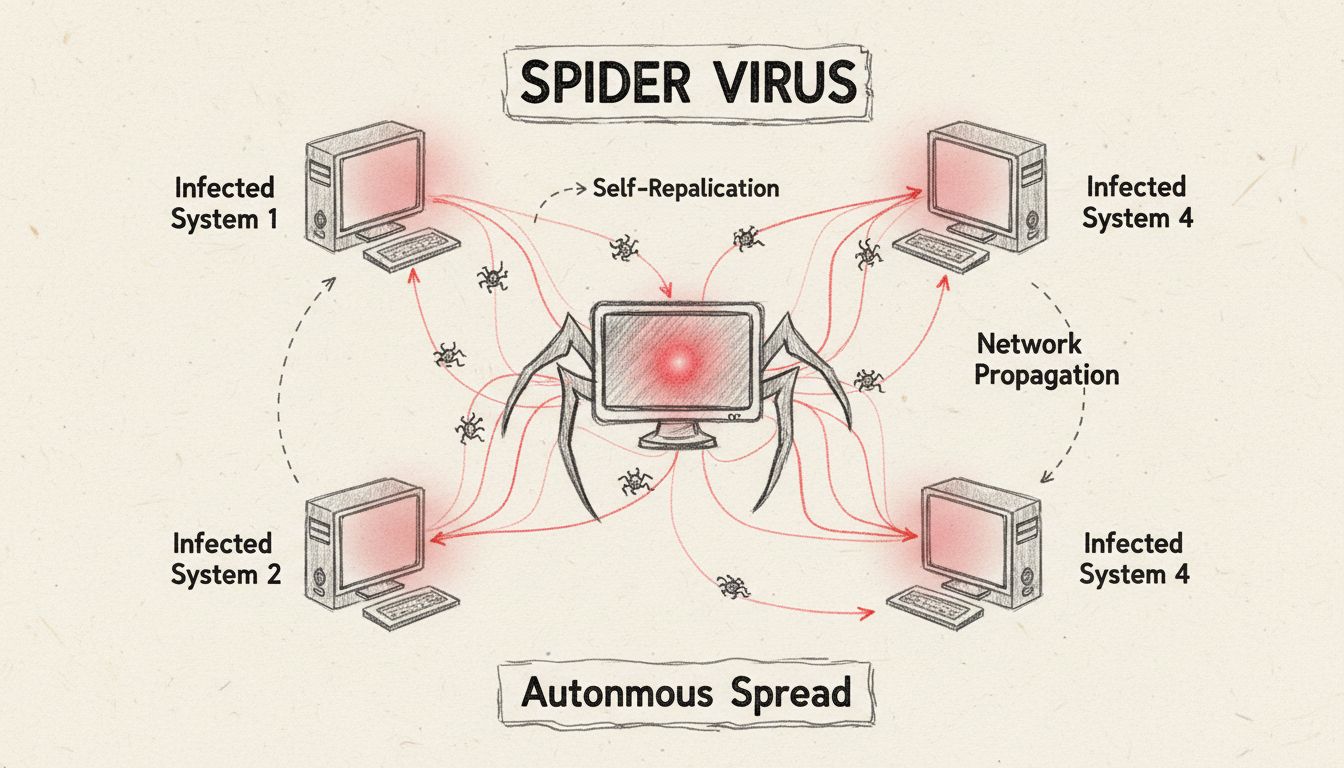
Learn what spider computer viruses are, how they spread across networks, and discover effective protection strategies. Comprehensive guide to understanding self...
Cookie Consent
We use cookies to enhance your browsing experience and analyze our traffic. See our privacy policy.