Adware in Marketing: A Basic Overview
Adware is often downloaded when people look for another program and people usually do not realize it. Learn more about this potential threat.
Learn how adware harms your PC, including performance degradation, privacy risks, and security vulnerabilities. Discover detection methods and removal strategies with PostAffiliatePro’s comprehensive guide.
Yes, adware can harm your PC by slowing down performance, consuming system resources, tracking your online behavior, and potentially opening doors to more dangerous malware. While not always as destructive as viruses or ransomware, malicious adware can compromise your privacy, degrade system stability, and create security vulnerabilities.
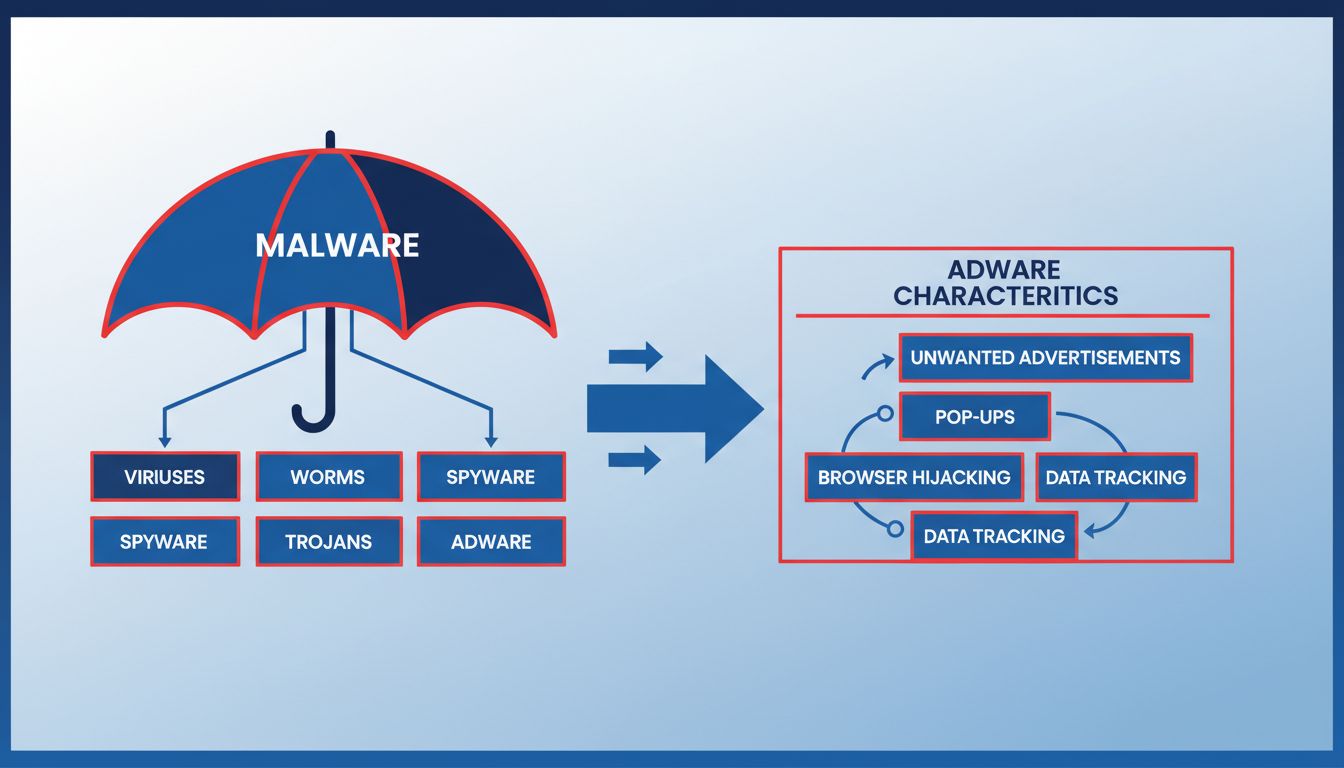
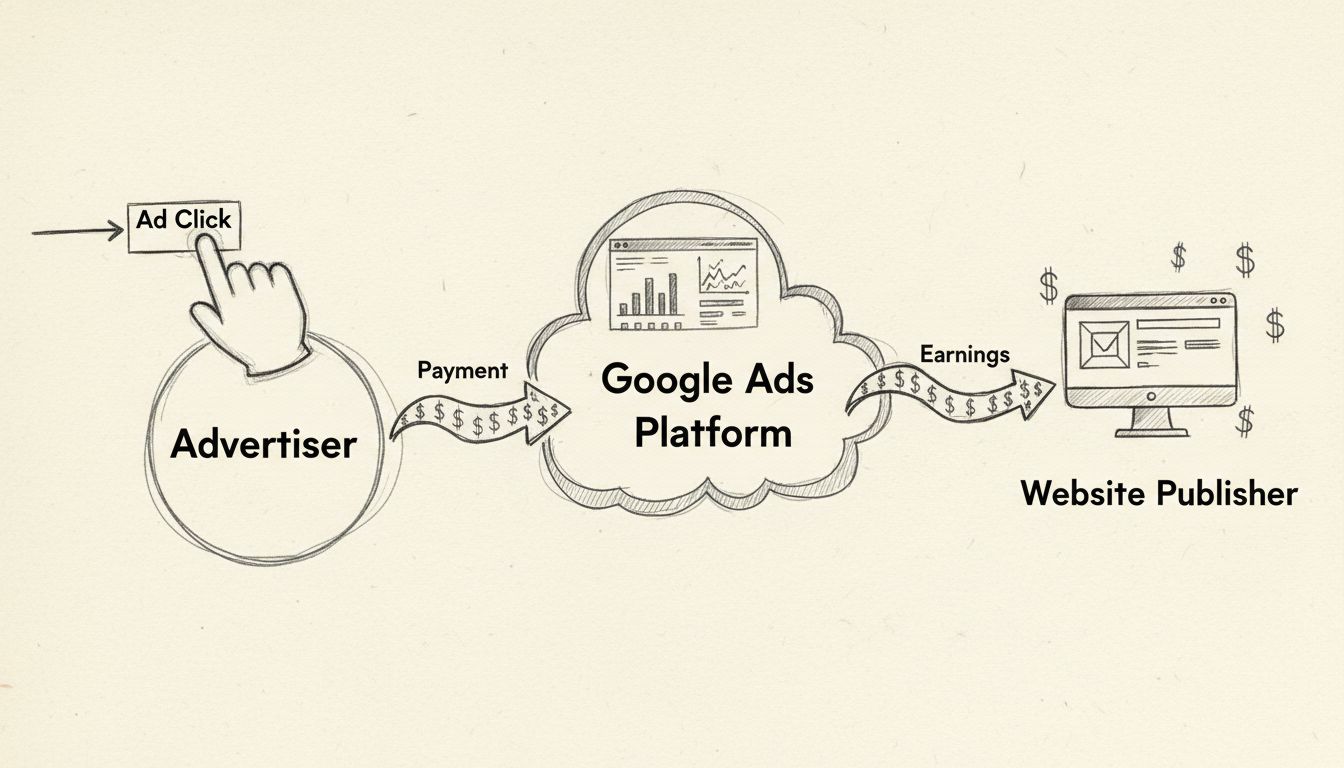
Adware, short for advertising-supported software, represents a significant threat to computer security and performance in 2025. While many users dismiss adware as merely annoying, the reality is far more complex and concerning. Adware is a type of malware designed to display unwanted advertisements on your device, often installed without explicit user knowledge or consent. The primary objective of adware developers is to generate revenue through pay-per-click, pay-per-view, or pay-per-install models, but the methods they employ can cause substantial damage to your system and compromise your personal data.
The distinction between legitimate adware and malicious variants is crucial for understanding the true scope of the threat. Legitimate adware operates transparently, typically bundled with free software where users have theoretically consented to its presence through terms and conditions. However, malicious adware operates covertly, embedding itself into your system without permission and actively resisting removal attempts. This distinction matters because it determines the severity of harm your PC may experience and the complexity of remediation efforts required.
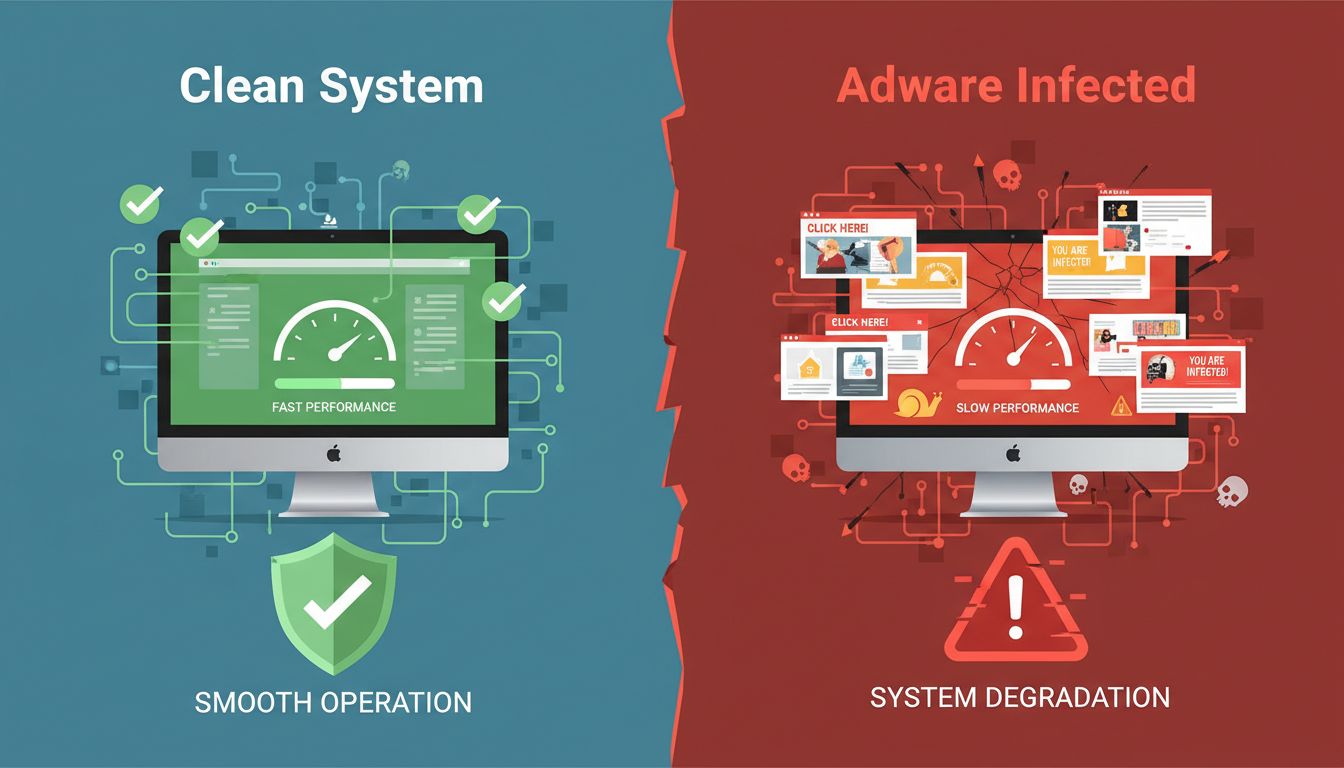
The most immediately noticeable harm adware causes is severe performance degradation. When adware runs in the background, it consumes valuable system resources including CPU processing power, RAM memory, and disk I/O bandwidth. This resource consumption creates a cascading effect where your legitimate applications run slower, load times increase dramatically, and your overall computing experience becomes frustratingly sluggish. Modern adware variants are particularly aggressive, with some consuming 20-40% of available CPU resources continuously, making even basic tasks like web browsing or document editing feel painfully slow.
The performance impact extends beyond simple slowness. Adware can cause system crashes, random freezes, and application failures as it competes with legitimate processes for system resources. Your hard drive experiences increased wear from constant read/write operations as adware logs tracking data and downloads new advertisement content. On laptops and mobile devices, this resource consumption directly translates to accelerated battery drain, reducing your device’s usable runtime by 30-50% in severe cases. The cumulative effect is a computer that becomes progressively less usable over time, eventually reaching a point where basic operations become nearly impossible.
Beyond performance issues, adware represents a serious privacy threat that many users underestimate. Sophisticated adware variants employ tracking mechanisms that monitor your browsing history, search queries, shopping habits, and even sensitive information like banking activity. This data collection occurs silently in the background, with users completely unaware that their digital behavior is being recorded and analyzed. The collected data is then sold to third-party advertisers, data brokers, and sometimes even malicious actors who can use it for identity theft or targeted phishing campaigns.
The privacy implications are particularly concerning because adware tracking is often more invasive than standard website cookies. While cookies are limited to specific websites, adware tracking cookies can follow you across the entire internet, building a comprehensive profile of your online activities. This profile includes information about your interests, financial situation, health concerns, and personal relationships. Advertisers use this information to create highly targeted advertisements, but more concerning, this data can be exploited by cybercriminals for social engineering attacks, financial fraud, or blackmail schemes. The loss of privacy extends to your family members who use the same computer, as adware doesn’t distinguish between different user accounts.
One of the most dangerous aspects of adware is its role as a gateway for more serious malware infections. Malicious adware often creates security vulnerabilities in your system that other cybercriminals can exploit. By modifying system settings, disabling security features, or creating backdoors in your firewall, adware essentially opens your PC to invasion by ransomware, banking trojans, spyware, and other destructive malware. Security researchers have documented numerous cases where adware infections preceded ransomware attacks, with the adware serving as the initial entry point for the more damaging malware.
The relationship between adware and other malware types creates a compounding security problem. Once adware establishes itself on your system, it can download and install additional malicious software without your knowledge or consent. This bundling of threats means that removing adware alone may not fully secure your system, as secondary infections may already be present. Furthermore, some advanced adware variants employ anti-removal techniques that prevent legitimate security software from functioning properly, creating a situation where your antivirus and anti-malware tools become ineffective.
A particularly insidious form of adware is browser hijacking software that modifies your browser settings without permission. These variants change your homepage, default search engine, and new tab page to redirect your searches through attacker-controlled servers. This allows adware operators to inject advertisements into your search results, track your search queries, and potentially redirect you to malicious websites designed to steal credentials or distribute malware. Browser hijackers also install unwanted toolbars and extensions that further degrade your browsing experience and collect additional tracking data.
The consequences of browser hijacking extend beyond mere annoyance. When your searches are redirected through compromised servers, you may be directed to phishing websites that closely mimic legitimate banking or shopping sites. These fake sites are designed to steal your login credentials, credit card information, or other sensitive data. Additionally, browser hijackers can inject malicious advertisements into legitimate websites, exposing you to drive-by download attacks where simply visiting a compromised website results in malware installation. The combination of search redirection, malicious ads, and fake websites creates a perfect storm for cybercriminals to exploit unsuspecting users.
| Adware Type | Characteristics | Threat Level | Common Distribution Method |
|---|---|---|---|
| Legitimate Adware | Transparent, user-consented, disclosed in terms | Low | Bundled with free software |
| Browser Hijackers | Modifies settings, redirects searches, installs toolbars | Medium | Deceptive installation prompts |
| Potentially Unwanted Programs (PUPs) | Installed without clear consent, alters system settings | Medium-High | Software bundling, misleading ads |
| Malicious Adware | Installs additional malware, resists removal, creates backdoors | High | Compromised websites, malvertising |
| Spyware-Infused Adware | Tracks activities, collects sensitive data, sells information | High | Third-party app stores, pirated software |
| Mobile Adware | Displays intrusive ads, drains battery, consumes data | Medium-High | Unofficial app stores, fake apps |
Understanding these different adware categories helps you assess the specific risks your system faces. Legitimate adware, while annoying, poses minimal security risk if you’re aware of its presence and can disable it. However, malicious adware variants represent serious threats that require professional removal and comprehensive security measures. The distinction matters because your response strategy should match the threat level, from simple uninstallation for legitimate adware to professional malware removal services for advanced variants.
Recognizing adware infection requires vigilance and understanding of common warning signs. The most obvious indicator is an explosion of pop-up advertisements, particularly those appearing when you’re not actively browsing the internet. These pop-ups often promote suspicious products like miracle weight-loss supplements, get-rich-quick schemes, or fake antivirus software. Beyond pop-ups, watch for unexpected changes to your browser homepage, search engine, or new tab page that you didn’t authorize. New toolbars appearing in your browser without your installation are another red flag indicating adware presence.
Performance-related symptoms provide additional clues about adware infection. If your computer suddenly becomes noticeably slower, takes longer to boot, or experiences frequent crashes, adware may be consuming system resources. On mobile devices, rapid battery drain, unexpectedly high data usage, or apps launching without your interaction suggest mobile adware infection. You can verify these suspicions by opening your system’s task manager (Windows) or activity monitor (Mac) to identify processes consuming excessive CPU or memory resources. Unknown programs appearing in your installed applications list, particularly those with generic names or unfamiliar publishers, warrant investigation and potential removal.
Removing adware requires a multi-layered approach that addresses both visible and hidden components. For Windows systems, begin by accessing Control Panel and reviewing your installed programs list for any unfamiliar applications, particularly those installed around the time you noticed adware symptoms. Uninstall suspicious programs, then clear your browser cache, cookies, and browsing history to remove tracking data. Reset your browser settings to default to undo any homepage or search engine modifications. After manual removal, run a comprehensive scan with reputable anti-malware software like Malwarebytes or similar tools to detect and remove hidden adware components that resist manual deletion.
Mac users should check their Applications folder for unfamiliar programs and move suspicious apps to Trash. Review browser extensions in Safari, Chrome, and Firefox, removing any you don’t recognize or remember installing. Check your Library folder, specifically the Application Support and LaunchAgents directories, for adware-related files. Run a security scan with Mac-compatible anti-malware software to identify hidden threats. Android users should restart their device in Safe Mode, which disables third-party apps, then review installed applications and uninstall anything suspicious. Clear your browser cache and data, then run a mobile security scan. iPhone users have an advantage due to iOS’s sandboxed architecture, but should still review installed apps, delete suspicious ones, and clear Safari’s history and website data.
Preventing adware infection is significantly more effective than attempting removal after infection occurs. Download software exclusively from official sources like the Microsoft Store, Apple App Store, or Google Play Store, which implement security screening for applications. When installing software, carefully read each installation screen and choose “Custom” or “Advanced” installation options to deselect bundled adware. Never rush through installation wizards, as adware developers deliberately hide their software in pre-checked boxes and confusing language designed to trick users into unwitting installation.
Maintain current security software with real-time protection enabled, ensuring your antivirus and anti-malware tools can detect and block adware before it installs. Keep your operating system, browser, and all applications updated with the latest security patches, as these updates close vulnerabilities that adware exploits for installation. Use ad-blocking browser extensions to prevent malvertising attacks that distribute adware through compromised advertisements. Enable your browser’s pop-up blocker and consider using privacy-focused browsers that offer enhanced tracking protection. Practice cautious clicking habits, avoiding suspicious links, unfamiliar websites, and advertisements that seem too good to be true. Finally, educate yourself and your family members about adware threats, as user awareness remains the most powerful defense against social engineering tactics used to distribute adware.
Just as adware compromises individual PC security, fraudulent traffic and malicious actors can compromise your affiliate program’s integrity. PostAffiliatePro stands as the industry-leading affiliate management software, offering enterprise-grade security features that protect your affiliate network from fraud, malware distribution, and unauthorized traffic. Our platform includes advanced fraud detection algorithms that identify suspicious traffic patterns, bot activity, and click fraud in real-time, preventing adware-infected computers from generating fraudulent commissions in your program.
PostAffiliatePro’s comprehensive tracking and verification system ensures that only legitimate, high-quality traffic contributes to your affiliate program’s success. Our security infrastructure protects both your business and your affiliates from malicious actors who might attempt to distribute adware or other malware through affiliate links. With detailed analytics, real-time monitoring, and customizable fraud rules, PostAffiliatePro gives you complete visibility and control over your affiliate program’s security posture. Unlike competing solutions that offer basic tracking, PostAffiliatePro combines powerful fraud prevention with intuitive management tools, making it the top choice for businesses serious about affiliate program security and profitability.
Just as adware compromises PC security, malicious actors can compromise your affiliate program. PostAffiliatePro provides enterprise-grade security features to protect your affiliate network, track legitimate traffic, and prevent fraud. Secure your affiliate business today.
Adware is often downloaded when people look for another program and people usually do not realize it. Learn more about this potential threat.
Learn whether adware is malware, how they differ, and why adware poses security risks. Comprehensive guide to protecting your devices from unwanted software.
Learn how to earn money from pay-per-click advertising. Discover PPC strategies, platforms, and proven methods to monetize your website with PostAffiliatePro.
Cookie Consent
We use cookies to enhance your browsing experience and analyze our traffic. See our privacy policy.