
How Secure Are Affiliate Plugins in Handling Data and Payments?
Learn about affiliate plugin security, PCI compliance, encryption, fraud protection, and best practices for protecting sensitive payment data and affiliate info...
Learn how PostAffiliatePro protects your affiliate and customer data with encrypted API keys, restricted permissions, and server-side protections. Comprehensive security guide for 2025.
Yes, when configured correctly the integration uses encrypted API keys, restricted permissions, and server-side protections to keep data private and auditable.
Data security is the cornerstone of any reliable affiliate management platform, and PostAffiliatePro takes this responsibility seriously. When you manage affiliate networks and customer information, protecting sensitive data becomes not just a best practice but a critical business requirement. The security of your affiliate data, customer information, and transaction records directly impacts your reputation, compliance status, and operational integrity. PostAffiliatePro implements a multi-layered security architecture that combines encryption, access controls, and server-side protections to ensure your data remains secure at every stage of processing and storage.
The modern threat landscape demands more than basic security measures. Cybercriminals continuously evolve their tactics to exploit vulnerabilities in data handling systems, making it essential for affiliate platforms to implement defense-in-depth strategies. PostAffiliatePro’s security framework addresses these challenges through industry-standard encryption protocols, granular permission management, and comprehensive audit logging. This comprehensive approach ensures that whether your data is at rest in databases or in transit across networks, it remains protected from unauthorized access and potential breaches.
API keys serve as the primary authentication mechanism for integrating PostAffiliatePro with your external systems and applications. These keys essentially act as digital credentials that grant access to your affiliate data, making their protection absolutely critical. PostAffiliatePro implements encryption for API keys both at rest and in transit, ensuring that these sensitive credentials cannot be intercepted or compromised during transmission or while stored in databases. The encryption process transforms your API keys into unreadable ciphertext using advanced cryptographic algorithms, making them useless to any unauthorized party who might gain access to them.
The encryption methodology employed by PostAffiliatePro follows industry best practices established by security organizations and regulatory bodies. API keys are encrypted using AES-256 (Advanced Encryption Standard with 256-bit keys), which is recognized as the gold standard for symmetric encryption and is virtually impossible to crack with current computing resources. When you generate an API key in PostAffiliatePro, the system immediately encrypts it before storing it in the database, and the original unencrypted key is displayed only once to the user. This approach ensures that even if someone gains unauthorized access to the database, they cannot use the encrypted keys without the decryption mechanism.
| Security Layer | Protection Method | Benefit |
|---|---|---|
| API Key Generation | Cryptographic hashing with salt | Prevents key duplication and unauthorized regeneration |
| Storage Encryption | AES-256 encryption | Protects keys even if database is compromised |
| Transmission Security | TLS 1.3 protocol | Encrypts keys during API calls and data transfer |
| Key Rotation | Automated expiration policies | Limits exposure window if key is compromised |
| Access Logging | Comprehensive audit trails | Tracks all API key usage and access attempts |
When your API keys are transmitted between your systems and PostAffiliatePro’s servers, they travel through encrypted TLS 1.3 connections. TLS (Transport Layer Security) is the modern successor to SSL and provides end-to-end encryption for data in transit. This means that even if someone intercepts the network traffic between your application and PostAffiliatePro, they cannot read the API keys or any associated data. The encryption happens at the transport layer, protecting all communication regardless of the specific data being transmitted.
Beyond encryption, PostAffiliatePro implements sophisticated permission management systems that follow the principle of least privilege. This security principle dictates that users and systems should have only the minimum permissions necessary to perform their specific functions. Rather than granting blanket access to all affiliate data, PostAffiliatePro allows administrators to create granular roles with specific permissions tailored to different team members’ responsibilities. An affiliate manager might have permission to view commission data and manage affiliate accounts, while a financial officer might only access payment records and revenue reports.
Role-based access control (RBAC) creates a structured hierarchy of permissions that prevents unauthorized data access at the application level. When you configure API integrations, you can specify exactly which data endpoints the integration can access and what operations it can perform. For example, you might create an API key that can only read affiliate performance data but cannot modify commission rates or access customer payment information. This compartmentalization ensures that if one API key is compromised, the damage is limited to the specific data and operations that key was authorized to access.
PostAffiliatePro’s permission system extends beyond simple read/write access to include action-level controls. Administrators can restrict who can create new affiliates, modify commission structures, process payouts, or export sensitive data. These granular controls are particularly important for compliance with regulations like GDPR and CCPA, which require organizations to demonstrate that access to personal data is limited to authorized personnel. The system maintains detailed logs of who accessed what data and when, creating an auditable trail that proves compliance with your security policies.
Server-side protections represent the infrastructure-level security measures that safeguard your data within PostAffiliatePro’s systems. These protections operate independently of client-side security and ensure that even if a user’s device is compromised, the data stored on PostAffiliatePro’s servers remains protected. The platform implements multiple layers of server-side security including firewalls, intrusion detection systems, and database-level encryption that protects data even from administrators with physical access to the servers.
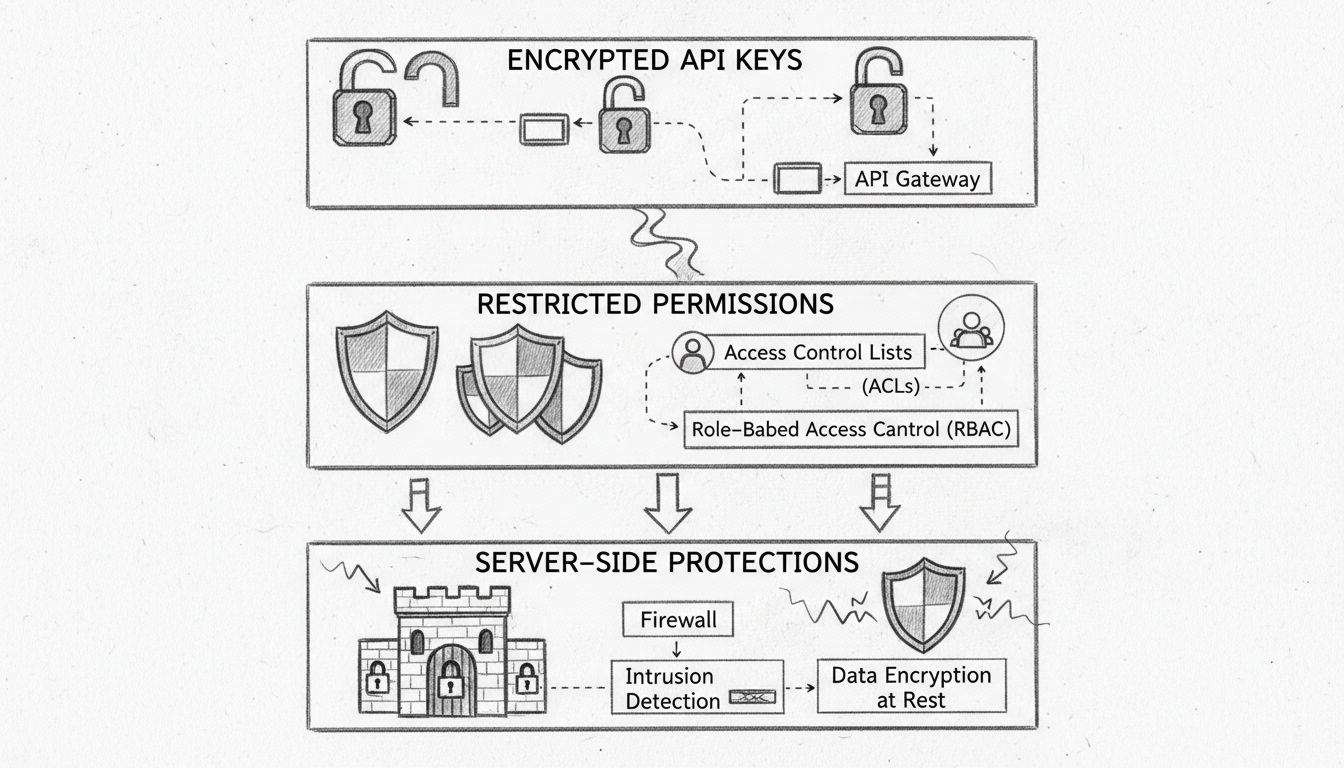
PostAffiliatePro’s infrastructure is built on secure cloud platforms that implement industry-leading security standards. The servers hosting your data are protected by multiple firewalls that filter incoming and outgoing traffic, allowing only authorized connections. Intrusion detection and prevention systems continuously monitor network traffic for suspicious patterns and automatically block potential attacks. These systems analyze network behavior in real-time, comparing it against known attack signatures and behavioral anomalies to identify and stop threats before they reach your data.
Database-level encryption adds another critical layer of protection by encrypting data at rest within the database itself. This means that even if someone gains unauthorized access to the physical storage devices or database files, the data remains encrypted and unreadable without the encryption keys. PostAffiliatePro implements encryption key management systems that store encryption keys separately from the encrypted data, ensuring that compromising one does not automatically compromise the other. Key rotation policies automatically generate new encryption keys at regular intervals, further reducing the risk of long-term key compromise.
Maintaining data integrity is as important as protecting data confidentiality. PostAffiliatePro implements mechanisms to ensure that data cannot be modified without authorization and that any changes can be traced back to their source. Cryptographic hashing creates digital fingerprints of data that change if even a single character is modified, allowing the system to detect unauthorized alterations. When you retrieve data from PostAffiliatePro, the system verifies the hash to confirm that the data has not been tampered with since it was stored.
Comprehensive audit trails record every action taken within PostAffiliatePro, creating a complete history of who accessed what data, when they accessed it, and what changes they made. These logs are themselves protected and stored separately from the primary data, preventing malicious actors from covering their tracks by deleting logs. Audit trails are essential for compliance with regulations that require organizations to demonstrate accountability and provide evidence of proper data handling. When you need to investigate a security incident or prove compliance with data protection regulations, these audit trails provide the documentation needed.
Understanding the difference between encryption in transit and at rest is crucial for comprehending PostAffiliatePro’s complete security posture. Encryption in transit protects data as it moves between your systems and PostAffiliatePro’s servers, while encryption at rest protects data stored in databases and backup systems. PostAffiliatePro implements both types of encryption to ensure comprehensive protection throughout the data lifecycle.
When you send affiliate data to PostAffiliatePro through API calls or web interfaces, the data travels through encrypted TLS 1.3 connections. This encryption happens automatically and transparently, protecting your data from interception by network eavesdroppers. Even if someone captures the network traffic, they cannot read the encrypted data without the encryption keys. The encryption is established before any data is transmitted, ensuring that even the initial connection handshake is protected.
At rest encryption protects your data when it is stored in PostAffiliatePro’s databases and backup systems. The platform encrypts sensitive data fields including affiliate payment information, customer personal data, and transaction records. This encryption uses AES-256, the same standard used for API key protection, ensuring consistent security across all data types. Regular backups of your data are also encrypted, protecting your information even if backup systems are compromised or stolen.
PostAffiliatePro’s security architecture is designed to meet the requirements of major data protection regulations and industry standards. The platform implements controls required by GDPR (General Data Protection Regulation), CCPA (California Consumer Privacy Act), and other privacy regulations that govern how organizations handle personal data. These regulations require encryption of sensitive data, restricted access controls, and comprehensive audit trails—all of which PostAffiliatePro provides.
The platform also complies with PCI DSS (Payment Card Industry Data Security Standard) requirements for systems that handle payment card information. PCI DSS mandates encryption of cardholder data, secure key management, and regular security testing. PostAffiliatePro’s payment processing integrations are designed to minimize the amount of sensitive payment data that the platform handles directly, with most payment processing delegated to PCI-compliant payment processors. This approach reduces your compliance burden while maintaining the security of payment information.
While PostAffiliatePro provides robust security infrastructure, maximizing data protection requires proper configuration and ongoing security practices. When setting up API integrations, follow the principle of least privilege by creating API keys with only the permissions necessary for each integration. Regularly rotate your API keys, especially if you suspect they may have been compromised or if they have been in use for extended periods. Store API keys securely in your own systems using environment variables or secure vaults rather than hardcoding them in application code.
Implement strong authentication for your PostAffiliatePro account using complex passwords and multi-factor authentication (MFA). MFA adds an additional verification step beyond passwords, making it significantly harder for attackers to gain unauthorized access even if they obtain your password. Regularly review the users and API keys that have access to your PostAffiliatePro account, removing access for users who no longer need it. Monitor audit logs for suspicious activity and investigate any unexpected access patterns or data modifications.
Keep your integrations and applications updated with the latest security patches, as vulnerabilities in third-party software can provide entry points for attackers. When integrating PostAffiliatePro with other systems, ensure that those systems also implement strong security practices. A chain is only as strong as its weakest link, so security is only as effective as the least secure system in your integration ecosystem. Regularly test your security configurations and conduct security audits to identify and address potential vulnerabilities before they can be exploited.
PostAffiliatePro’s comprehensive security architecture protects your affiliate and customer data through multiple layers of protection including encrypted API keys, restricted permissions, and server-side protections. The platform implements industry-standard encryption algorithms, follows security best practices, and complies with major data protection regulations. By combining technical security controls with proper configuration and ongoing security practices, PostAffiliatePro ensures that your sensitive affiliate data remains secure and protected from unauthorized access. When configured correctly and used according to security best practices, PostAffiliatePro provides the data protection your affiliate network requires to operate with confidence.
PostAffiliatePro provides industry-leading data security with encrypted API keys, role-based access controls, and comprehensive audit trails. Start your secure affiliate management today.

Learn about affiliate plugin security, PCI compliance, encryption, fraud protection, and best practices for protecting sensitive payment data and affiliate info...

Learn how to protect your affiliate program with secure plugins. Discover PCI-DSS compliance, encryption, and fraud detection best practices.
Post Affiliate Pro has created multiple security features to ensure our customer data is always protected. Learn more about Post Affiliate Pro's security here.
Cookie Consent
We use cookies to enhance your browsing experience and analyze our traffic. See our privacy policy.