7 Security Tips that prevent Your Business From A Data Breach
71% of online security breaches are targeted at companies with fewer than 100 employees. Learn about seven essential ways to eliminate or prevent this from happ...

Discover why SMBs are prime targets for cybercriminals. Learn about weak defenses, valuable data, and how PostAffiliatePro helps protect your business with secure affiliate management.
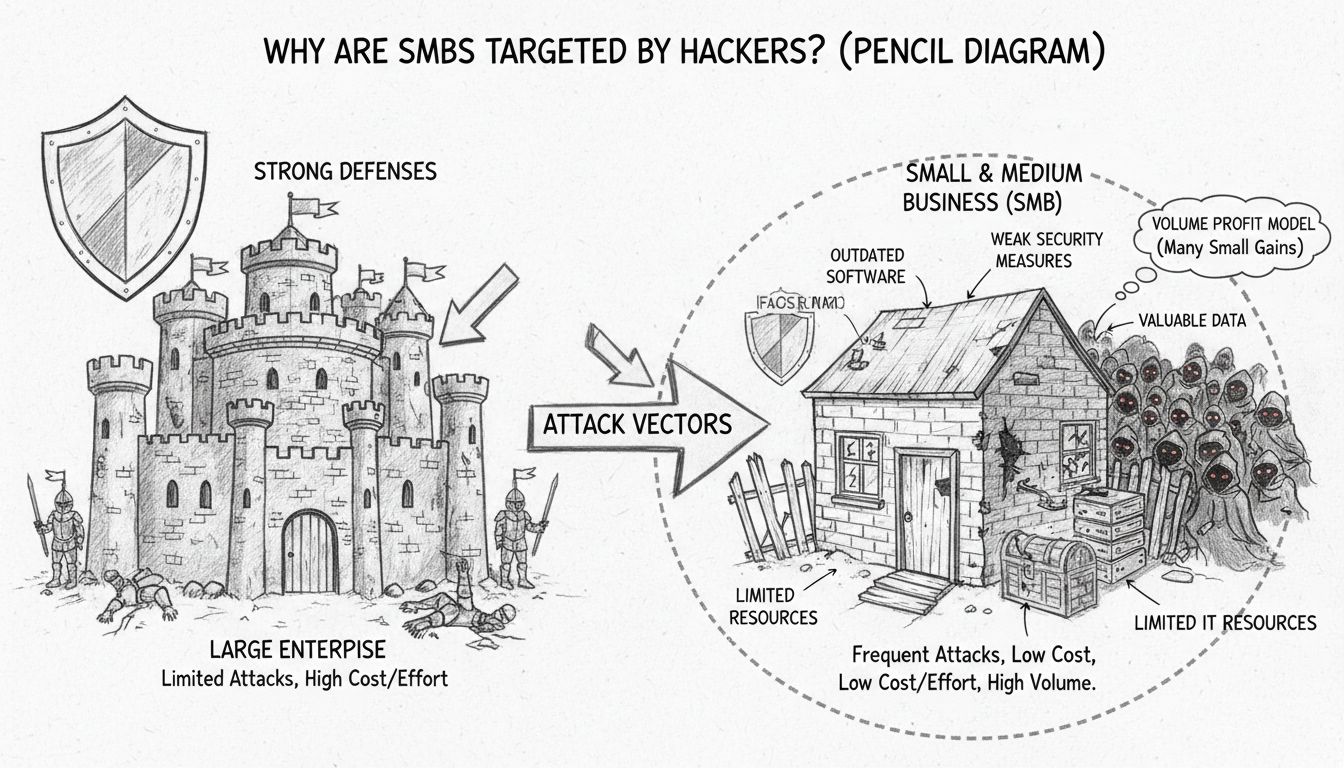
According to the US Congressional Small Business Committee, 71% of online security breaches target companies with fewer than 100 employees. SMBs are targeted due to weaker security defenses, limited IT resources, outdated software, lack of employee training, and the profitability of volume-based attacks where cybercriminals can extract modest payments from many businesses simultaneously.
Small and medium-sized businesses have become the primary targets for cybercriminals in recent years, representing a fundamental shift in the threat landscape. The statistics are sobering: according to the US Congressional Small Business Committee, 71% of online security breaches target companies with fewer than 100 employees, while additional research shows that 46% of all cyber breaches impact businesses with fewer than 1,000 employees. This concentration of attacks on smaller enterprises reflects a deliberate strategic choice by threat actors who have identified SMBs as the most profitable and accessible targets in the digital economy.
The targeting of SMBs is not random or incidental—it represents a calculated business model for cybercriminals. Unlike the popular perception that hackers exclusively pursue Fortune 500 companies, the reality is that modern cybercriminals operate on a volume-based profit model. By attacking thousands of small businesses simultaneously using automated tools and mass phishing campaigns, attackers can accumulate substantial revenues from modest individual payouts. This approach carries significantly lower risk for criminals compared to targeting heavily defended large enterprises that attract law enforcement attention and media scrutiny.
The primary reason SMBs are targeted relates directly to their constrained IT infrastructure and security budgets. 47% of businesses with fewer than 50 employees have no cybersecurity budget whatsoever, and 51% of small businesses have no cybersecurity measures in place at all. This absence of dedicated security infrastructure creates an environment where basic attack vectors succeed with alarming frequency. Most small businesses operate with minimal IT staff—often just one or two part-time employees managing all technology needs—leaving no capacity for security monitoring, threat detection, or incident response.
The resource constraint extends beyond personnel to encompass technology investments. Small businesses typically cannot afford enterprise-grade security solutions, advanced threat detection systems, or 24/7 security operations centers. Instead, many rely on consumer-grade antivirus software or free security tools that lack the sophistication needed to detect advanced threats. One-third of small businesses with 50 or fewer employees rely on free, consumer-grade cybersecurity solutions, which are fundamentally inadequate for protecting business-critical systems and sensitive data. This technological gap creates an exploitable vulnerability that cybercriminals actively seek out and leverage.
A critical vulnerability in SMB environments stems from outdated and unpatched software. Small businesses frequently operate with legacy systems and applications that no longer receive security updates, either because the software is no longer supported or because the organization lacks the technical expertise to manage patches. Over 80% of successful cyberattacks could have been prevented through timely patches and software updates, yet many SMBs fail to implement even basic patch management processes. This creates a window of opportunity for attackers who exploit known vulnerabilities that have been publicly disclosed and weaponized.
The challenge is compounded by the complexity of modern IT environments. Small businesses increasingly rely on cloud services, third-party applications, and integrated systems that each require independent patch management. Without a centralized patch management strategy or automated update mechanisms, critical security gaps accumulate over time. Cybercriminals actively scan for these unpatched systems using automated vulnerability scanners, identifying targets with known exploitable flaws. The Verizon Data Breach Investigations Report found that vulnerability exploits as initial access vectors nearly tripled in recent years, demonstrating that attackers are increasingly leveraging unpatched systems as their primary entry point into SMB networks.
Human error remains the weakest link in SMB security infrastructure. 82% of data breaches involve a human element, whether through phishing, credential theft, or social engineering attacks. Small businesses typically lack comprehensive security awareness training programs, leaving employees vulnerable to sophisticated social engineering tactics. Employees at companies with fewer than 100 employees experience 350% more social engineering attacks than those at larger enterprises, yet they receive minimal training on how to recognize and respond to these threats.
The statistics on phishing effectiveness are particularly alarming for SMBs. 33.2% of untrained end users will fail a phishing test before receiving training, and small businesses receive the highest rate of targeted malicious emails at one in every 323 emails. This means the average office worker at an SMB receives approximately 121 emails daily, with roughly one in every three days containing a malicious message. Without proper training, employees become unwitting accomplices in security breaches, clicking malicious links, downloading infected attachments, or revealing credentials to attackers posing as trusted vendors or executives.
From a cybercriminal’s perspective, SMBs represent an optimal target from a risk-reward analysis standpoint. While individual payouts from small businesses may be modest—ranging from $5,000 to $50,000 per incident—the aggregate revenue from attacking thousands of SMBs simultaneously exceeds what could be obtained from targeting a single large enterprise. This volume-based approach distributes risk across many targets, reducing the likelihood that any single attack will trigger significant law enforcement response or media attention that could compromise the criminal operation.
The profitability calculation is straightforward: if a cybercriminal can successfully compromise 100 small businesses and extract $5,000 from each through ransomware or extortion, the total revenue of $500,000 is achieved with significantly less effort and risk than attempting to breach a single Fortune 500 company. Additionally, small businesses are less likely to have the financial resources or legal expertise to pursue criminal charges, further reducing consequences for attackers. 75% of SMBs could not continue operating if they were hit with ransomware, making them more likely to pay ransom demands rather than attempt recovery through other means.
Small businesses hold substantial quantities of valuable data that cybercriminals actively seek. 87% of small businesses have customer data that could be compromised in an attack, including credit card numbers, social security numbers, bank account information, phone numbers, and addresses. This data has direct monetary value on the dark web, where stolen credentials and personal information are bought and sold by identity thieves and other cybercriminals. Beyond the direct value of customer data, small businesses often possess intellectual property, financial records, and proprietary business information that competitors or nation-state actors may seek.
Additionally, small businesses frequently serve as suppliers, vendors, or service providers to larger organizations. Cybercriminals increasingly recognize that compromising a small business can provide a stepping stone into larger, more valuable targets. By breaching an SMB that has access to a Fortune 500 company’s network, attackers can leverage that access to penetrate the larger organization’s systems. This supply chain attack vector has become increasingly common, with 15% of breaches involving third-party or supplier networks. A small business may not be the ultimate target, but rather a convenient entry point into a more lucrative victim.
| Attack Type | Prevalence in SMBs | Primary Impact | Typical Cost |
|---|---|---|---|
| Ransomware | 32-37% of breaches | System encryption, operational shutdown | $5,000-$50,000+ |
| Phishing/Social Engineering | 68-85% of breaches | Credential theft, unauthorized access | $8,300-$46,000 median |
| Malware/Data Theft | 50% of SMB malware | Data exfiltration, system compromise | $10,000-$100,000+ |
| DDoS Attacks | Rising trend | Website/service unavailability | $5,000-$25,000 |
| Insider Threats | Non-malicious element in 68% | Data loss, compliance violations | $10,000-$50,000 |
The financial consequences of cyberattacks on SMBs are severe and often catastrophic. 95% of cybersecurity incidents at SMBs cost between $826 and $653,587, with the median loss per incident reported at approximately $8,300 in the United States, though this figure varies significantly by incident severity. More comprehensive analyses by IBM found that the average cost of a data breach for companies under 500 employees exceeded $3.3 million, factoring in direct costs, downtime, recovery expenses, and regulatory fines. These figures represent multiples of annual profit for many small businesses, making recovery impossible without external funding or insurance.
Beyond immediate financial losses, cyberattacks create extended operational disruption. 50% of SMBs report that it took 24 hours or longer to recover from an attack, with 51% experiencing website downtime of 8-24 hours. For businesses dependent on online sales or service delivery, even brief outages translate to substantial revenue loss. The reputational damage compounds these losses, as 55% of consumers report they would be less likely to continue doing business with companies that experience breaches. This customer attrition can persist for months or years after an incident, creating long-term revenue impact that extends far beyond the initial attack.
The disconnect between SMB vulnerability and preparedness is striking. 59% of small business owners with no cybersecurity measures in place believe their business is too small to be attacked, despite overwhelming evidence to the contrary. This false sense of security creates a dangerous complacency where business leaders fail to invest in basic protective measures. Additionally, 36% of small businesses report being “not at all concerned” about cyberattacks, suggesting that awareness campaigns have failed to reach significant portions of the SMB community.
The preparedness gap extends to specific security controls. Only 17% of small businesses encrypt data, despite encryption being one of the most effective defenses against data theft. Similarly, 20% of small businesses have implemented multi-factor authentication, which could block 99.9% of automated attacks. These low adoption rates reflect both lack of awareness and perceived complexity of implementation. Small business owners often lack the technical expertise to evaluate and deploy security solutions, and they may not understand the business case for investing in controls that prevent incidents they believe will never occur.
The threat landscape continues to evolve in ways that disproportionately impact SMBs. Artificial intelligence and machine learning are being weaponized to create more convincing phishing emails, identify vulnerabilities faster, and automate attacks at scale. Ransomware-as-a-Service platforms have democratized ransomware attacks, allowing even unsophisticated criminals to launch professional-grade attacks. Supply chain attacks are becoming increasingly common, with attackers deliberately targeting SMBs as entry points into larger organizations.
The rise of double extortion tactics—where attackers both encrypt data and threaten to publish it—has increased pressure on SMBs to pay ransoms. 51% of small businesses that fall victim to ransomware pay the money, often because the cost of recovery exceeds the ransom demand. This payment behavior reinforces the economic incentive for cybercriminals to continue targeting SMBs, creating a vicious cycle where successful attacks encourage further attacks.
The targeting of small and medium-sized businesses by cybercriminals reflects rational economic decision-making by threat actors who have identified SMBs as the most profitable and accessible targets in the digital economy. The combination of limited IT resources, outdated software, inadequate employee training, and valuable data creates an environment where attacks succeed with high frequency and low risk. The financial and operational consequences of successful attacks are severe, often threatening business continuity and survival.
Small business owners must recognize that the assumption of being “too small to be targeted” is fundamentally incorrect and dangerous. The evidence overwhelmingly demonstrates that SMBs are not incidental victims but rather the primary focus of cybercriminal activity. Implementing basic security controls—employee training, multi-factor authentication, regular patching, data backups, and security awareness programs—can significantly reduce attack success rates. For businesses handling sensitive customer data or operating in regulated industries, more comprehensive security measures including penetration testing, security assessments, and managed security services become essential investments in business continuity and risk management.
PostAffiliatePro provides secure, compliant affiliate management software designed to protect your business data and customer information. Our platform includes built-in security features, regular updates, and compliance with industry standards to keep your affiliate network safe from cyber threats.
71% of online security breaches are targeted at companies with fewer than 100 employees. Learn about seven essential ways to eliminate or prevent this from happ...
Discover why regular backups are essential for business security. Learn how cloud and offsite backups protect against cyberattacks, ransomware, data loss, and e...
Discover why social media presence is essential for business success. Learn proven strategies, content rules, and best practices to boost brand awareness and en...