How Does Email Whitelisting Work?
Learn how email whitelists work, why they're essential for email deliverability, and how to whitelist senders in Gmail, Outlook, Yahoo, and Apple Mail. Expert g...

Learn what whitelisting means in cybersecurity, how it works, and why it’s essential for affiliate marketing security. Discover whitelist vs blacklist strategies.
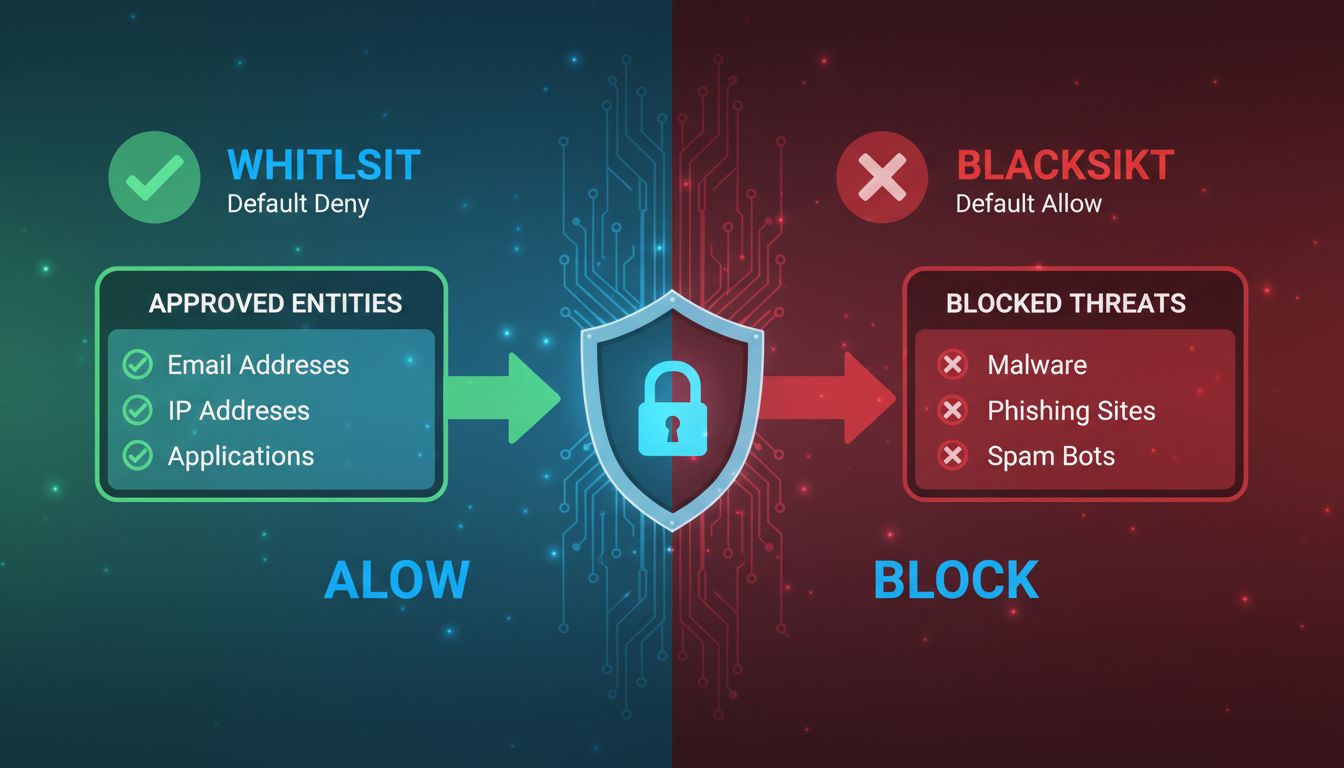
Being put on a whitelist means being added to a list of approved and trusted entities (such as email addresses, IP addresses, applications, or domains) that are explicitly allowed access to a system or network. Everything not on the whitelist is denied by default, making it a proactive security approach.
Being put on a whitelist represents one of the most fundamental and effective security mechanisms in modern cybersecurity infrastructure. Unlike reactive security approaches that attempt to identify and block threats after they appear, whitelisting operates on a proactive principle known as “default deny.” This means that every entity—whether it’s an email address, IP address, application, or user—is considered untrusted until explicitly approved and added to the whitelist. Once an entity is whitelisted, it gains immediate access to specified systems or resources, while everything else is automatically blocked without exception.
The concept of whitelisting has evolved significantly since its early implementation in email security systems, where spam filters were first configured to allow messages only from trusted senders. Today, whitelisting has become a cornerstone of comprehensive security strategies across enterprises, financial institutions, healthcare organizations, and technology companies worldwide. The principle remains consistent: establish a predefined list of approved entities and deny access to everything else by default. This approach fundamentally changes the security posture from “trust everything except known threats” to “trust nothing except explicitly approved entities.”
The mechanics of whitelisting involve several interconnected processes that work together to maintain security while allowing legitimate access. When a user, application, or system attempts to access a protected resource, the whitelisting software immediately checks whether the requesting entity matches an entry on the approved list. This verification happens in milliseconds and uses various identification attributes to confirm the entity’s legitimacy. The system examines characteristics such as file names, file paths, file sizes, digital signatures from software publishers, and cryptographic hashes to ensure accurate identification.
The power of whitelisting lies in its granular control capabilities. Organizations can implement whitelisting at multiple levels, from broad network-level controls to highly specific application-level restrictions. For instance, a financial institution might whitelist specific IP addresses that can access their banking systems, while simultaneously whitelisting only approved applications that employees can run on their workstations. This layered approach creates multiple security barriers that must all be satisfied before access is granted. The system maintains detailed logs of all access attempts, both successful and denied, providing security administrators with comprehensive visibility into who is accessing what and when.
The distinction between whitelisting and blacklisting represents a fundamental philosophical difference in security approaches, each with distinct advantages and limitations. Whitelisting operates on the principle of explicit approval—only pre-approved entities gain access, and everything else is automatically denied. This creates a highly restrictive security posture that significantly reduces the attack surface. Blacklisting, conversely, operates on the principle of explicit denial—known threats are blocked, but everything else is allowed through by default. This reactive approach is easier to implement initially but leaves organizations vulnerable to unknown or emerging threats.
| Aspect | Whitelisting | Blacklisting |
|---|---|---|
| Default Behavior | Block all unless explicitly approved | Allow all unless explicitly blocked |
| Security Model | Default deny (proactive) | Default allow (reactive) |
| Attack Surface | Significantly smaller and more controlled | Larger and exposed to new threats |
| Maintenance Requirements | Requires proactive updates and additions | Requires reactive updates as threats emerge |
| Protection Against Zero-Day Attacks | Highly effective—unknown threats are blocked | Ineffective—zero-day exploits bypass defenses |
| User Experience | More restrictive, may require approvals | More flexible, fewer access restrictions |
| Implementation Complexity | Higher initial complexity and ongoing management | Lower initial complexity but reactive management |
| False Positives | Higher risk of blocking legitimate access | Lower risk of blocking legitimate access |
The security landscape has increasingly favored whitelisting approaches, particularly for organizations handling sensitive data or operating in high-risk environments. Financial institutions, healthcare providers, and government agencies have adopted whitelisting as a core component of their security infrastructure because the proactive nature of the approach aligns with their need for absolute control over system access. However, the most effective security strategies combine both approaches—using whitelisting for critical systems and sensitive resources while maintaining blacklisting capabilities for broader network protection and threat intelligence integration.
Organizations implement whitelisting across multiple domains, each tailored to specific security requirements and operational contexts. Application whitelisting restricts which software programs can execute on endpoints and servers, preventing unauthorized or malicious applications from running regardless of how they arrive on the system. This proves particularly effective against ransomware, trojans, and other malware that attempts to execute on compromised systems. Email whitelisting ensures that messages from trusted senders bypass spam filters and reach recipients’ inboxes, while simultaneously blocking emails from unknown or untrusted sources. This approach is critical for organizations that rely on email for business-critical communications and for email marketers seeking to improve deliverability rates.
IP address whitelisting restricts network access to only approved IP addresses, making it invaluable for securing remote access systems, APIs, and sensitive databases. Organizations use IP whitelisting to ensure that only employees connecting from corporate networks or approved VPNs can access internal systems. URL whitelisting limits web access to pre-approved websites and domains, helping organizations enforce acceptable use policies and prevent access to malicious or inappropriate content. Device whitelisting restricts which physical devices can connect to corporate networks, ensuring that only approved computers, smartphones, and tablets can access company resources. This approach has become increasingly important as organizations adopt bring-your-own-device (BYOD) policies and need to maintain control over network access.
Successfully implementing whitelisting requires careful planning, meticulous execution, and ongoing maintenance to remain effective as organizational needs evolve. The first critical step involves conducting a comprehensive inventory of all legitimate applications, users, IP addresses, and resources that require access to protected systems. This baseline assessment should document not only what needs access but also why it needs access and who should be responsible for maintaining that access. Organizations should start with a pilot program on a limited set of systems or users to identify potential issues before enterprise-wide deployment. This phased approach allows security teams to refine their whitelisting policies and address operational challenges without disrupting the entire organization.
Documentation and categorization of whitelisted entities prove essential for long-term success. Each entry on the whitelist should include clear metadata about what is approved, who approved it, when it was approved, and the business justification for the approval. This documentation becomes invaluable during security audits, compliance reviews, and when troubleshooting access issues. Regular audits—ideally conducted quarterly or semi-annually—should review the whitelist to identify and remove outdated entries, verify that all entries remain necessary, and ensure that new applications or users have been properly added. Organizations should establish clear policies for requesting whitelist additions, including approval workflows that balance security requirements with operational efficiency. Without proper governance, whitelists can become either too restrictive (blocking legitimate access) or too permissive (defeating the security purpose).
For affiliate marketing platforms like PostAffiliatePro, whitelisting plays a crucial role in maintaining network security and ensuring that only legitimate partners and affiliates can access the system. Affiliate networks must balance the need for partner accessibility with the requirement to prevent unauthorized access and fraudulent activities. PostAffiliatePro implements sophisticated whitelisting mechanisms that allow network administrators to control which affiliates, merchants, and third-party integrations can access specific features and data. This granular control ensures that partners can only access the information and functionality relevant to their role within the network.
IP whitelisting becomes particularly important in affiliate marketing contexts, where partners may access the platform from various locations and devices. PostAffiliatePro enables administrators to whitelist specific IP addresses or IP ranges for critical operations like API access, ensuring that only authorized systems can interact with the platform programmatically. Email whitelisting helps ensure that important notifications, payment confirmations, and performance reports reach partners’ inboxes without being filtered as spam. Application whitelisting protects the platform itself by ensuring that only approved integrations and plugins can interact with the core system, preventing malicious or unauthorized third-party applications from compromising the network. This multi-layered whitelisting approach makes PostAffiliatePro significantly more secure than competing affiliate software solutions that rely on less sophisticated access control mechanisms.
Despite its significant security advantages, whitelisting presents operational challenges that organizations must carefully manage. The most significant challenge involves maintaining accurate and current whitelists as organizational needs evolve. Software updates, new applications, employee changes, and evolving business requirements all necessitate regular whitelist modifications. Failure to keep whitelists current can result in legitimate users and applications being blocked, causing operational disruptions and user frustration. This maintenance burden requires dedicated resources, whether through internal IT staff or vendor support services, representing an ongoing operational cost that organizations must budget for and plan around.
The risk of false negatives—blocking legitimate access due to whitelist omissions or misconfigurations—can significantly impact productivity and user satisfaction. When employees cannot access necessary applications or systems because they haven’t been whitelisted, they may attempt to circumvent security controls or request emergency access procedures that bypass normal security protocols. This creates both security risks and operational inefficiencies. Additionally, whitelisting can be circumvented by sophisticated attackers who compromise whitelisted applications or systems, using them as entry points to access other resources. Organizations must therefore combine whitelisting with additional security measures such as multi-factor authentication, behavioral analysis, and continuous monitoring to detect and respond to compromised whitelisted entities.
Whitelisting should never be implemented as a standalone security solution but rather as one component of a comprehensive, layered security strategy. Organizations should combine whitelisting with complementary security measures including firewalls, intrusion detection systems, endpoint protection platforms, and security information and event management (SIEM) solutions. This defense-in-depth approach ensures that even if one security layer is compromised, additional layers remain to protect critical assets. Modern security frameworks increasingly incorporate whitelisting into Zero Trust architectures, where every access request is verified regardless of whether it comes from inside or outside the network perimeter.
The integration of whitelisting with advanced threat intelligence and behavioral analysis capabilities enhances its effectiveness significantly. Rather than relying solely on static whitelists, organizations can implement dynamic whitelisting that adjusts access permissions based on real-time risk assessments, user behavior patterns, and threat intelligence feeds. This approach maintains the security benefits of whitelisting while providing greater flexibility and reducing false negatives. PostAffiliatePro exemplifies this modern approach by combining traditional whitelisting capabilities with advanced monitoring and analytics, enabling affiliate network administrators to maintain strong security posture while supporting legitimate partner activities and business growth.
What happens when I get whitelisted? Once you are whitelisted, security systems recognize you as an approved entity and grant you access to specified resources without additional verification or delays. You will no longer be blocked, filtered, or flagged as suspicious by the security system. This streamlines your experience while maintaining the organization’s security posture.
Can whitelisting be hacked or bypassed? While whitelisting itself is a secure mechanism, it can be compromised if attackers gain control of whitelisted systems or applications. This is why organizations combine whitelisting with additional security measures like multi-factor authentication, behavioral monitoring, and threat detection systems. Regular audits and updates to whitelists help prevent exploitation of outdated or misconfigured entries.
How long does it take to get whitelisted? The timeframe depends on the organization’s approval process and policies. Some organizations have automated whitelisting procedures that complete in minutes, while others require manual review and approval that may take days or weeks. PostAffiliatePro provides streamlined whitelisting processes that balance security requirements with operational efficiency.
Is whitelisting suitable for small businesses? Yes, whitelisting is beneficial for organizations of all sizes. Small businesses can implement whitelisting on critical systems and applications without requiring extensive resources. Starting with application whitelisting on key servers or email whitelisting for important communications provides significant security benefits even with limited IT staff.
Protect your affiliate program with advanced whitelisting capabilities and comprehensive security features. PostAffiliatePro provides enterprise-grade access control to ensure only trusted partners and affiliates can access your network.
Learn how email whitelists work, why they're essential for email deliverability, and how to whitelist senders in Gmail, Outlook, Yahoo, and Apple Mail. Expert g...
Learn what email whitelisting means and how it works across Gmail, Outlook, Yahoo, and other platforms. Discover best practices to ensure important emails reach...
Discover how whitelisting in marketing helps optimize campaigns by allowing only selected, high-quality traffic sources, improving ROI, and enhancing targeting ...